
Como copiar chaveiros RFID e cartões de acesso
Índice
Como copiar chaveiros RFID e cartões de acesso: um guia completo
Mas e se perderes o teu Chaveiros RFID ou precisa de uma cópia extra para a família ou funcionários? Este guia explica como funciona a cópia, quais chips podem ser duplicados e quais precauções legais e de segurança devem ser seguidas.
Lista de verificação rápida: como funciona a cópia
Antes de mergulhar, aqui está um resumo simples de 4 passos que pode seguir:
Digitalizar → Gravar → Testar → Registar
- Digitalize o seu original Chaveiros RFID usando uma copiadora RFID USB compatível.
- Grave os dados armazenados numa etiqueta ou cartão RFID em branco.
- Teste a nova etiqueta na sua porta ou leitor.
- Registe-o com o administrador do sistema, se necessário.
⚠️ Nota: Copie apenas chaveiros RFID ou cartões de acesso que você possui ou está autorizado a duplicar. A duplicação não autorizada pode ser ilegal e comprometer a segurança do sistema.
O que é um chaveiro RFID e como funciona?
Um Chaveiro RFID é um pequeno dispositivo sem fios que utiliza identificação por radiofrequência (RFID) para comunicar com um leitor. Quando tocado num leitor, transmite um número de identificação único que o sistema de acesso reconhece e concede a entrada.
Principais funcionalidades
- Conveniência: Entrada sem chaves, com um simples toque.
- Durabilidade: Resiste ao uso diário.
- Acesso personalizável: Programado para utilizadores ou áreas específicas.
Estes porta-chaves e Cartões RFID são utilizados em apartamentos, escritórios, sistemas de estacionamento e escolas.
Por que copiar chaveiros RFID ou cartões de acesso?
- Conveniência: Dê aos familiares ou funcionários os seus próprios porta-chaves.
- Cópia de segurança: Evite bloqueios caso o original seja perdido.
- Acesso partilhado: Simplifique a entrada para a equipa de limpeza, hóspedes ou alugueres de curta duração.
Ter um cartão RFID de reserva garante a continuidade do acesso sem ter de esperar pela substituição.
Compreender os tipos de chips e a dificuldade de cópia
Nem todos os chaveiros RFID podem ser clonados. A cópia depende da frequência e do tipo de chip dentro do cartão ou chaveiro.
1. Baixa frequência (LF) de 125 kHz – EM4100 / HID Prox
- Utilização comum: sistemas de construção mais antigos.
- Cópia: relativamente fácil com uma copiadora RFID USB básica e etiquetas em branco de 125 kHz.
- Processo: digitalizar → escrever → testar → registar.
2. Alta frequência (HF) de 13,56 MHz – MIFARE Classic
- Utilização comum: escritórios, escolas, cartões de transporte.
- Cópia: possível apenas se a encriptação for fraca ou inexistente.
- Ferramentas: uma copiadora avançada compatível com MIFARE Classic.
3. DESFire / HID iCLASS / SEOS (cartões inteligentes encriptados)
- Utilização comum: sistemas empresariais ou governamentais.
- Cópia: normalmente não é possível sem credenciais de administrador.
- Melhores práticas: Solicite uma segunda via oficial ao gerente do seu prédio.
Dica: Verifique a etiqueta de frequência no seu cartão RFID ou digitalize-o com um leitor RFID para identificar o tipo de chip antes de tentar duplicá-lo.

Ferramentas necessárias
Para copiar corretamente um chaveiro ou cartão RFID, prepare o seguinte:
- Copiadora ou duplicadora RFID – para ler e gravar dados.
- Etiquetas ou cartões RFID em branco – para criar novas cópias.
- Chaveiro RFID original – a credencial de origem.
- (Opcional) Aplicação NFC para smartphone – utilização limitada para algumas etiquetas de 13,56 MHz.
Você pode navegar Etiquetas RFID em branco de 125 kHz e Cartões RFID para controlo de acesso de fornecedores confiáveis.
Posso copiar um chaveiro RFID com o meu telemóvel?
Alguns smartphones com NFC podem ler e emular cartões RFID de 13,56 MHz, mas não podem clonar fobs encriptados.
- Funciona com: chips MIFARE Classic ou NTAG desprotegidos.
- Não funciona com: HID iCLASS, SEOS ou DESFire.
- Hardware extra: pode ser necessário para gravar em cartões físicos.
Riscos de segurança e como se manter seguro
Copiar chaveiros RFID sem supervisão pode criar problemas de segurança:
- Acesso não autorizado: as duplicatas podem ser utilizadas indevidamente.
- Dados não encriptados: Os fobs mais antigos são mais fáceis de clonar.
- Roubo de dados: leitores inseguros podem vazar informações.
Melhores práticas: - Use cartões RFID criptografados ou seguros.
- Alterne as credenciais de acesso regularmente.
- Monitorize os registos de entrada para detetar padrões invulgares.
Aumentando a segurança do controlo de acesso
Para fortalecer o seu sistema:
- Atualize para chaveiros criptografados (MIFARE DESFire ou HID iCLASS).
- Ative o acesso de dois fatores: combinar RFID com PIN ou biometria.
- Acompanhar a atividade do utilizador: utilizar registos de software para detetar anomalias.
“Um chaveiro RFID devidamente encriptado reduz o risco de clonagem e protege toda a sua instalação.”
RFID vs. NFC: Comparação rápida
| Recurso | RFID | NFC |
|---|---|---|
| Faixa | Até vários metros | Alguns centímetros |
| Utilização típica | Controlo de acesso, logística | Pagamentos móveis, cartões inteligentes |
| Dificuldade de duplicação | Moderado a elevado | Muito alto (devido à encriptação) |
Ambos utilizam radiofrequência, mas a NFC é mais segura e normalmente utilizada em smartphones e sistemas de pagamento, enquanto os chaveiros RFID são otimizados para entrada em portas e identificação.
Criptografia em cartões RFID modernos
A encriptação protege a comunicação entre o cartão RFID e o leitor, tornando a cópia não autorizada praticamente impossível.
Benefícios:
- Evita a duplicação de dados.
- Preserva a integridade dos dados.
- Protege o seu sistema contra ataques futuros.
Mudar para cartões RFID encriptados é uma das formas mais fáceis de impedir cópias não autorizadas.
Perguntas frequentes sobre chaveiros RFID e cartões de acesso
Como posso saber se meu chaveiro está criptografado?
Os fobs encriptados geralmente requerem software proprietário ou leitores especiais. Se uma fotocopiadora básica não conseguir lê-lo, é provável que esteja encriptado.
Posso copiar um chaveiro RFID em casa?
Sim, é possível com uma copiadora RFID compatível e etiquetas em branco, mas apenas se tiver permissão para duplicá-las.
Qual é a diferença entre RFID e NFC?
A RFID tem um alcance maior e várias bandas de frequência; a NFC tem um alcance curto e é usada principalmente em smartphones.
É legal copiar um cartão de acesso RFID?
Copiar sem autorização pode violar regras de privacidade ou propriedade. Obtenha sempre a aprovação do proprietário do sistema.
Quais são as frequências comuns?
125 kHz (LF) e 13,56 MHz (HF) são as frequências mais comuns para chaveiros e cartões de acesso.
Conclusão
Os chaveiros RFID e os cartões de acesso são ferramentas poderosas para segurança e conveniência — mas duplicá-los requer conhecimento sobre tipos de chips, ferramentas e limites legais.
Em caso de dúvida, procure a ajuda de um técnico certificado em RFID ou solicite uma substituição oficial à administração do seu edifício.
Precisa de chaveiros RFID, cartões de acesso ou copiadoras confiáveis para o seu projeto?
Fale com os nossos especialistas em RFID para amostras, preços ou aconselhamento técnico.
📩 Envie-nos um e-mail para [email protected]

Raio Zhou
Este artigo foi escrito por Ray Zhou, um especialista em tecnologia RFID com mais de 10 anos de experiência no sector.
Comentários
Produtos quentes
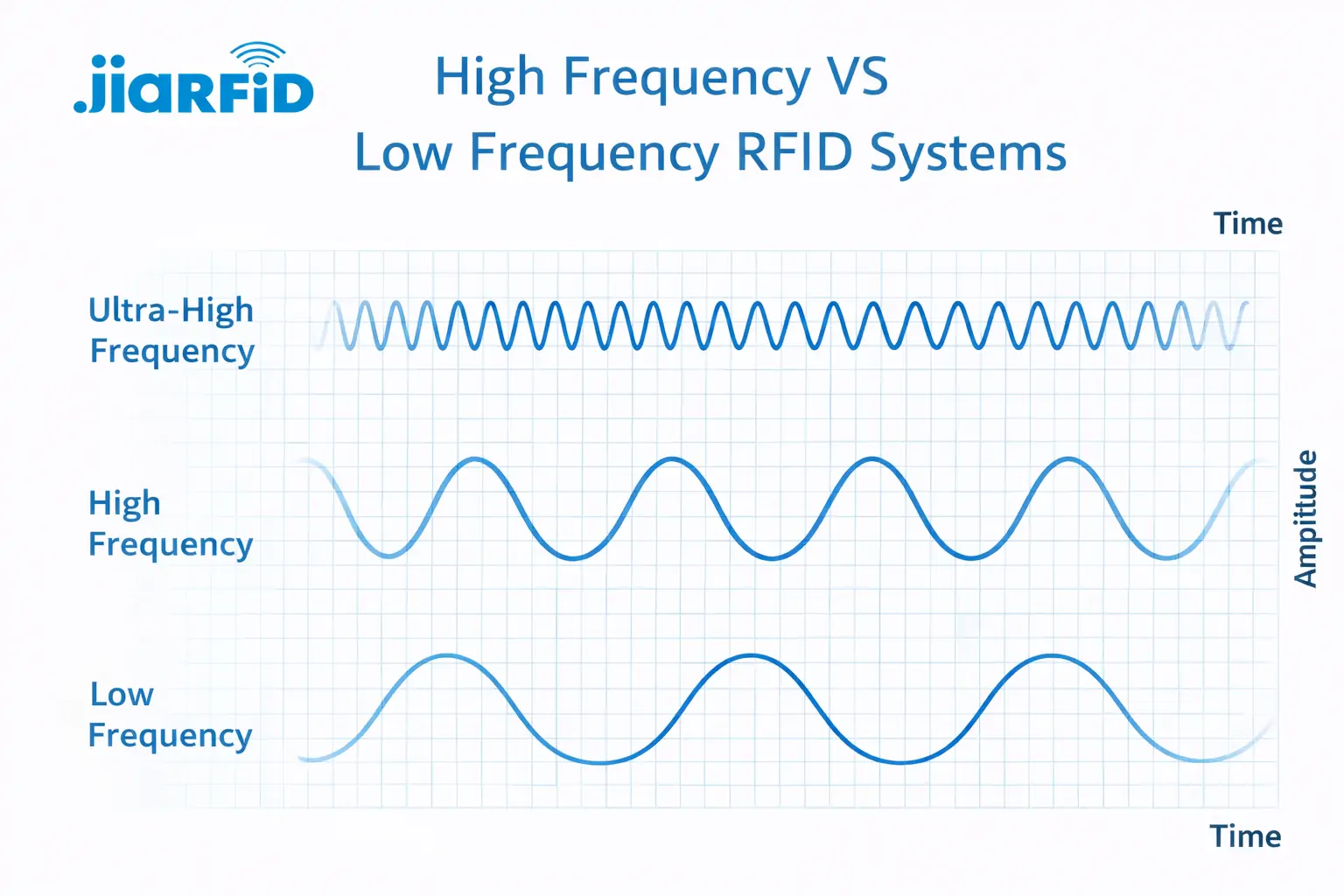
RFID de baixa frequência vs. RFID de alta frequência: as principais diferenças
A RFID de baixa frequência e a RFID de alta frequência são ambas tecnologias RFID indutivas que se baseiam no acoplamento de campos magnéticos entre o
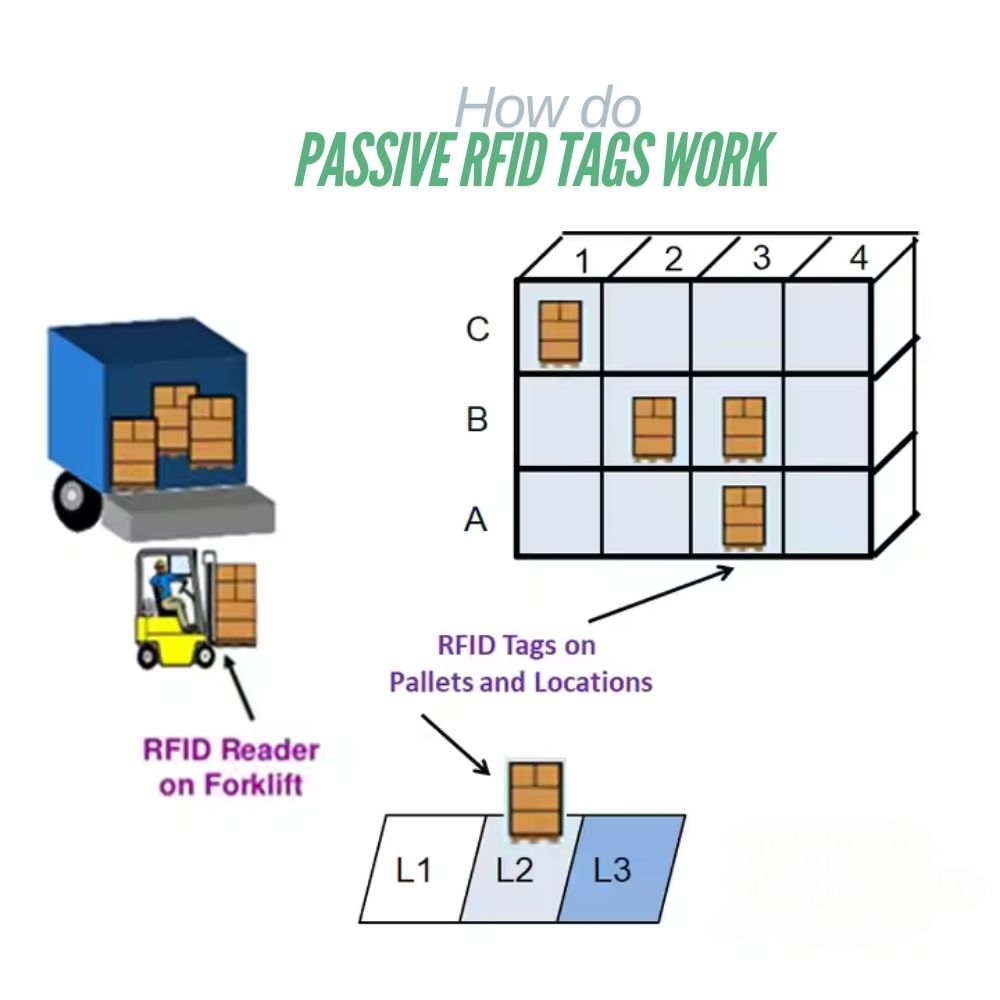
O que são etiquetas RFID passivas e como funcionam
Uma etiqueta RFID passiva é uma etiqueta RFID que não tem fonte de alimentação interna. Não pode funcionar ou transmitir por

Explicação sobre cartões e etiquetas RFID de 13,56 MHz: Tudo o que deve saber
A tecnologia RFID desempenha um papel importante nos modernos sistemas de identificação e de intercâmbio de dados. Entre as diferentes frequências RFID, 13,56 MHz
RFID na logística: como eliminar erros de encaminhamento e falhas nas etiquetas RFID
A RFID na logística é mais do que apenas uma ferramenta para acelerar processos. Tornou-se uma parte fundamental do funcionamento das cadeias de abastecimento modernas.
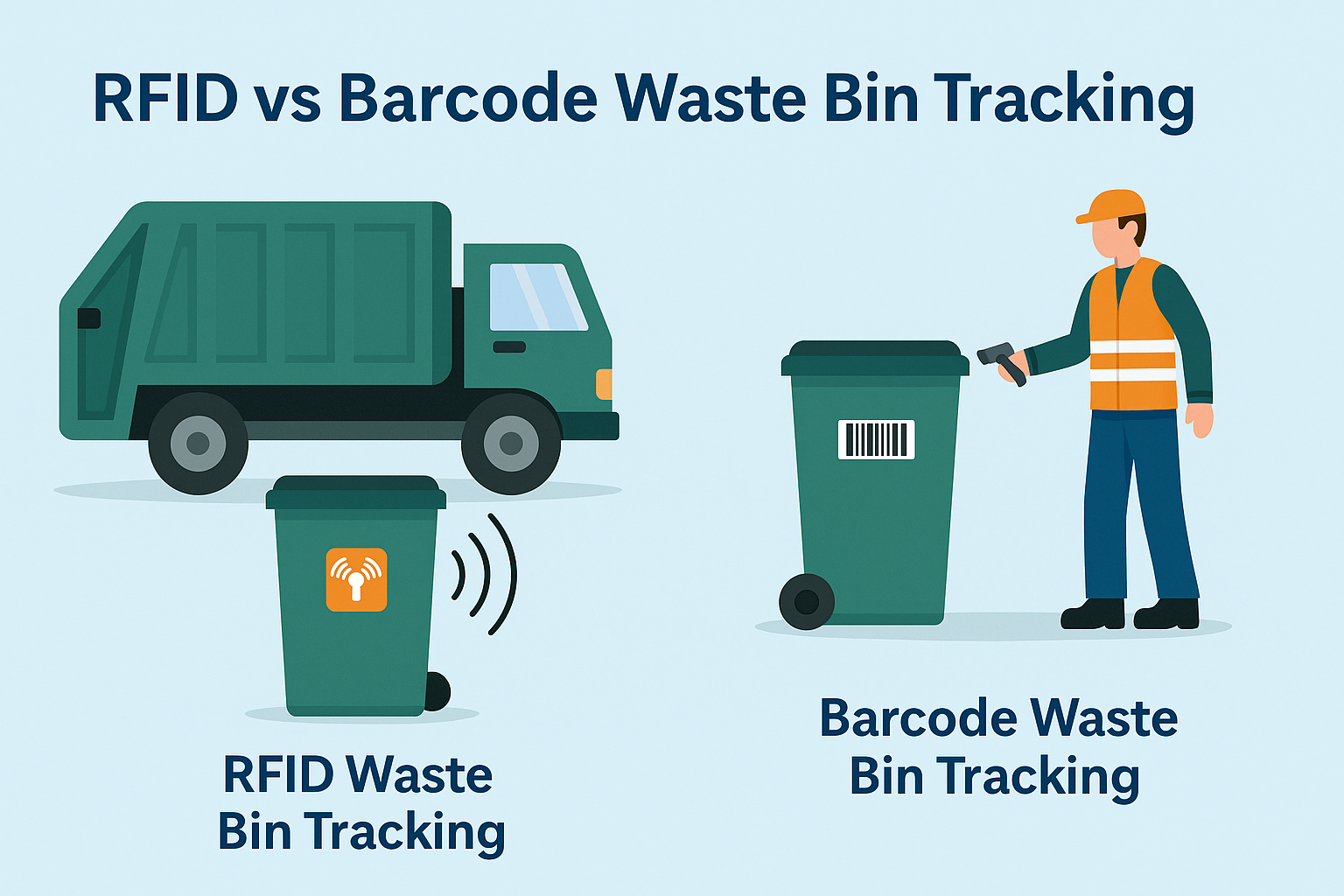
O que é a gestão de resíduos por RFID
Imagine uma cidade onde todas as lixeiras falam — não literalmente — mas através de um pequeno chip que informa ao sistema quando estão cheias, quando são esvaziadas e para onde vão. É isso que a gestão de resíduos por RFID está a fazer hoje.

O que são vedantes de parafuso e suas aplicações? | Guia completo
No comércio global e na logística, os selos de segurança desempenham um papel crucial para garantir a segurança e a conformidade da carga. Estes pequenos mas poderosos dispositivos foram concebidos para bloquear contentores de transporte, reboques e portas de carga com um mecanismo inviolável.
Etiquetas
BLOGS RELACIONADOS
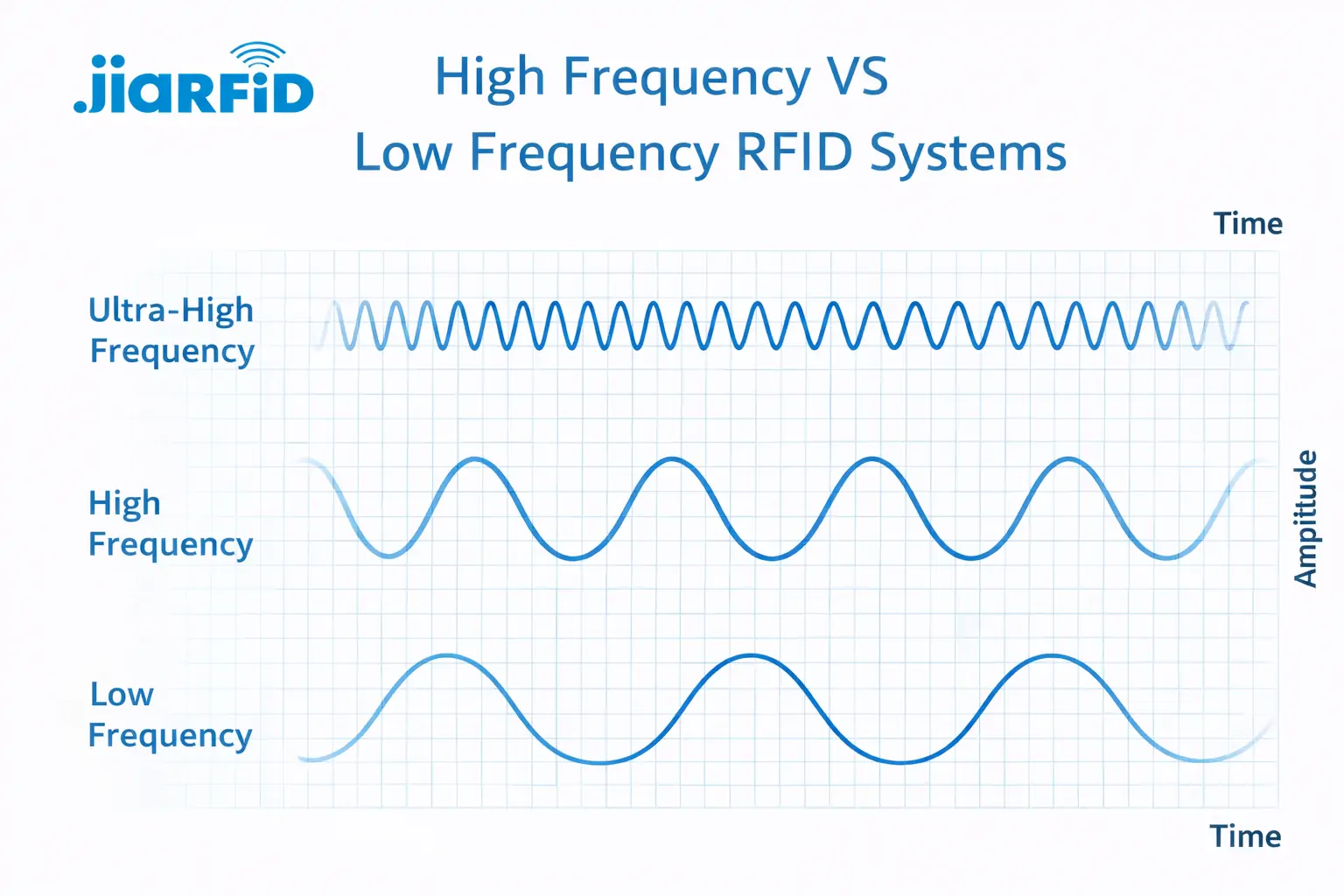
RFID de baixa frequência vs. RFID de alta frequência: as principais diferenças
A RFID de baixa frequência e a RFID de alta frequência são ambas tecnologias RFID indutivas que se baseiam no acoplamento de campos magnéticos entre o
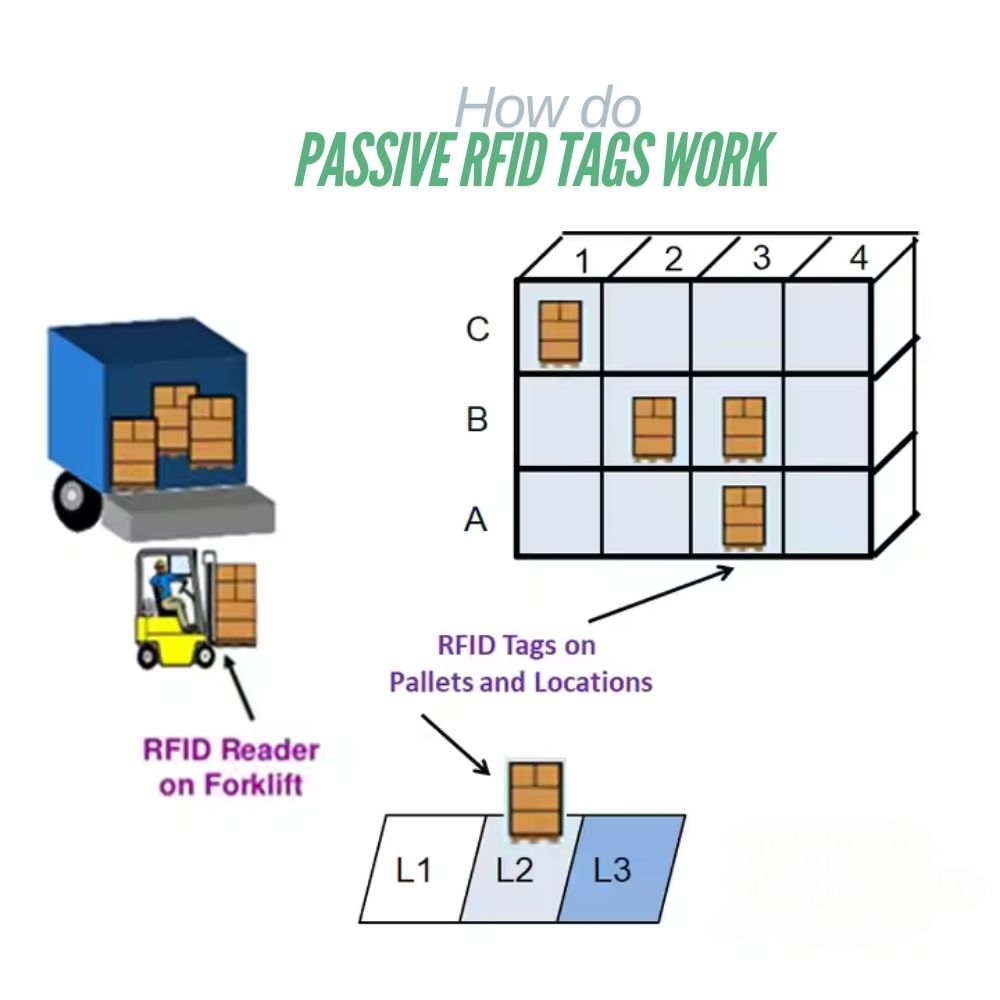
O que são etiquetas RFID passivas e como funcionam
Uma etiqueta RFID passiva é uma etiqueta RFID que não tem fonte de alimentação interna. Não pode funcionar ou transmitir por

Explicação sobre cartões e etiquetas RFID de 13,56 MHz: Tudo o que deve saber
A tecnologia RFID desempenha um papel importante nos modernos sistemas de identificação e de intercâmbio de dados. Entre as diferentes frequências RFID, 13,56 MHz




