
Wie speichern RFID-Tags Daten?
Inhaltsverzeichnis
Einführung
Dieses Verfahren zu verstehen, ist nicht nur akademisch interessant. Für Ingenieure, die intelligente Lieferketten entwerfen, Entwickler, die RFID-integrierte Apps erstellen, und IT-Manager, die die Nachverfolgung großer Anlagen überwachen, sind die grundlegenden Mechanismen des RFID-Speichers, der Datenkodierung und der Sicherheitsprotokolle entscheidend für die Leistung, Interoperabilität und Datenintegrität.
Was ist RFID und wie funktioniert es?
Was ist RFID?
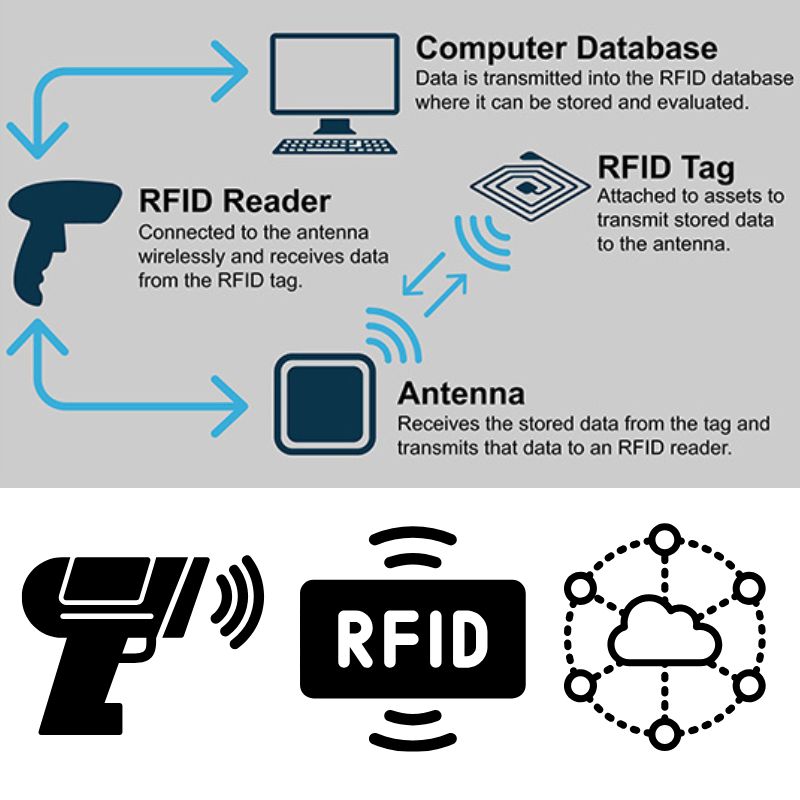
RFID (Radio Frequency Identification) ist eine drahtlose Technologie, die Objekte mithilfe elektromagnetischer Felder automatisch identifiziert und verfolgt. Im Gegensatz zu Barcodes benötigt RFID keine direkte Sichtverbindung und kann mehr Daten direkt auf dem Tag speichern.
Wichtige Komponenten eines RFID-Systems
- RFID-Tag (Transponder): Ein Chip und eine Antenne, die in ein Etikett oder einen Gegenstand eingebettet sind und Daten speichern.
- RFID-Lesegerät (Abfragegerät): Sendet ein Funksignal, um den Tag zu aktivieren und dessen Daten zu empfangen.
- Middleware/Systemsoftware: Verarbeitet, speichert und leitet Daten an Datenbanken oder Anwendungen weiter.
Wie die Datenübertragung funktioniert
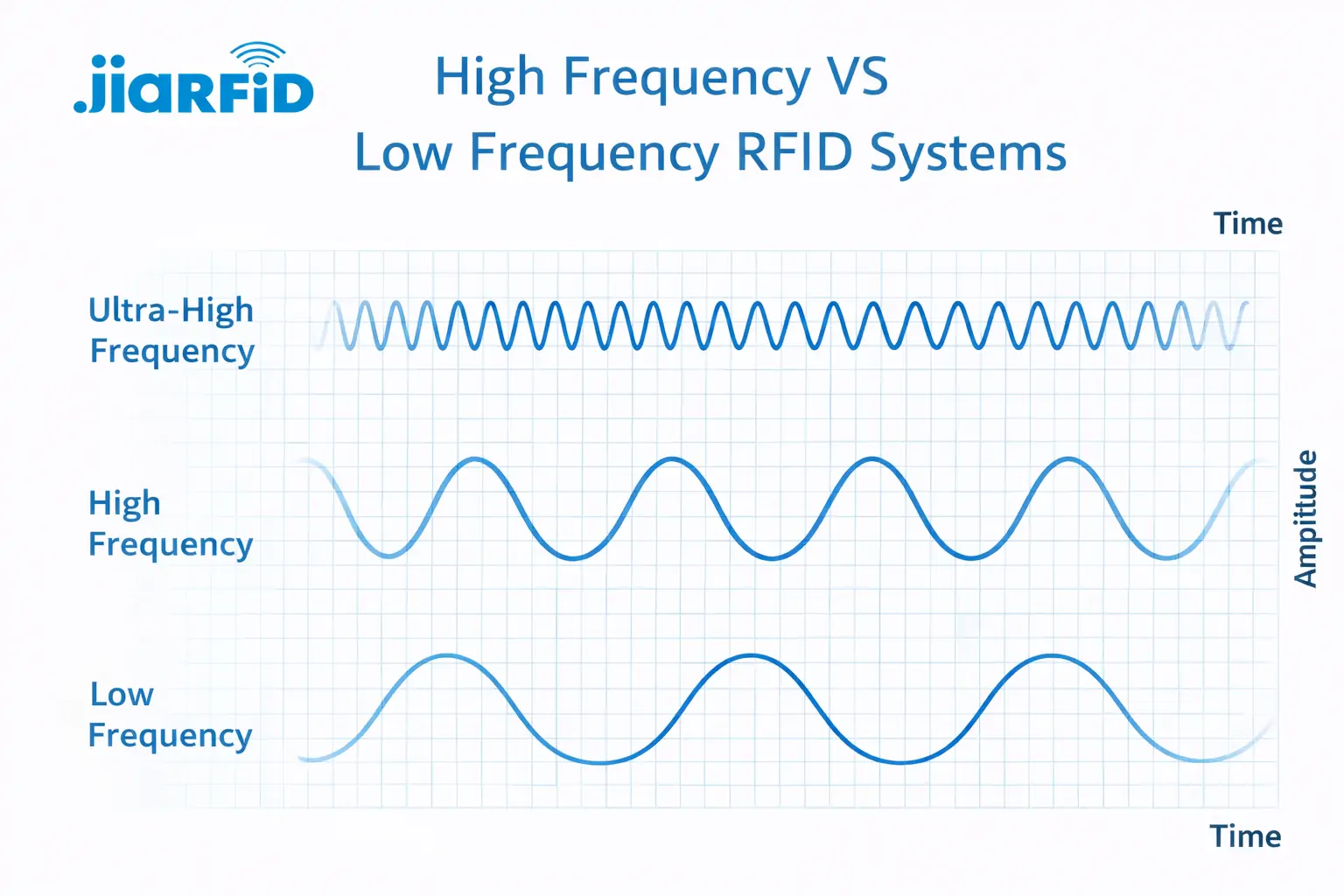
Wenn der RFID-Leser ein Hochfrequenzsignal aussendet, empfängt die Antenne des Tags dieses Signal und versorgt den Chip mit Strom (sofern es sich um einen passiven Chip handelt). Der Chip moduliert dann die gespeicherten Daten und sendet sie zurück an den Leser. Diese Kommunikation variiert je nach Frequenz:
- LF (Low Frequency): Kurze Reichweite, gut geeignet für die Ortung von Tieren.
- HF (Hochfrequenz): Häufig bei NFC und Smartcards.
- UHF (Ultra High Frequency): Größere Reichweite, höhere Lesegeschwindigkeiten – ideal für die Logistik.
Technischer Tipp: Passive UHF-Tags werden am häufigsten in industriellen Lieferketten verwendet, da sie kostengünstig sind und eine Reichweite von bis zu mehreren Metern haben.
Einsteigerhandbuch zur Programmierung von RFID-Tags
Das Programmieren von RFID-Tags kann leistungsstarke Funktionen freischalten – von der Anpassung von Produktdaten bis hin zur sicheren Zugangskontrolle. Es stehen zwar viele Tools und Ansätze zur Verfügung, die konkrete Methode hängt jedoch vom Tag-Typ, der Frequenz und der Anwendung ab.
Wir arbeiten derzeit an verifizierten Code-Beispielen und praktischen Anleitungen für die sichere und effektive Programmierung von RFID-Tags. Dieser Abschnitt wird in Kürze Folgendes enthalten:
- Praktische Tutorials zur Verwendung von Arduino mit RFID-Modulen.
- Kodierung von Daten mit TagWriter (Android) für NFC-kompatible Tags.
- Verwendung von RFID-SDKs und Desktop-Writern für Unternehmensanwendungen.
- Tipps zur Auswahl des richtigen Speicherformats (ASCII, HEX, EPC).
Möchten Sie jetzt beginnen? Wir empfehlen Ihnen, sich in der Zwischenzeit mit diesen Ressourcen vertraut zu machen:
- NXP TagWriter App– NFC-Kodierung für Android
- MFRC522 Arduino-Bibliothek auf GitHub– Open-Source-RFID-Lesegerät-Bibliothek
- [SDK oder Entwickler-Tools Ihres Hardware-Herstellers] für bestimmte Lesermodelle
Benötigen Sie Hilfe beim Schreiben von Daten auf Ihre RFID-Tags oder bei der Auswahl kompatibler Tools? Kontaktieren Sie unser technisches Team für personalisierte Unterstützung.
Wie RFID-Tags Daten intern speichern
Im Kern ist ein RFID-Tag ein winziges Speichergerät mit bestimmten Speicherbänken. Das Verständnis des internen Speicheraufbaus ist entscheidend, wenn man plant, welche Art von Daten gespeichert werden sollen – und wie viel.
Arten von Speicher in RFID-Tags
- ROM (Read-Only Memory): Daten, die während der Herstellung geschrieben werden. Sie können nicht geändert werden.
- EEPROM (Electrically Erasable): Wiederbeschreibbar; wird am häufigsten in modernen RFID-Systemen verwendet.
- RAM: Temporärer Speicher, der häufig bei aktiven Transaktionen verwendet wird.
Gängige Speichertypen
- Schreibgeschützt (RO): Kann nicht geändert werden. Wird für feste IDs verwendet.
- Lesen/Schreiben (RW): Kann mit kompatiblen Lesegeräten geändert werden.
- WORM (Write Once, Read Many): Nach der Programmierung sind die Daten gesperrt.
Speicherbänke in EPCglobal Gen2-Tags (UHF)
| Speicherbank | Inhalt | Beschreibbar? |
|---|---|---|
| EPÜ | Produkt-ID (typischerweise 96–128 Bit) | ✅ |
| TID | Eindeutige Tag-/Chip-Kennung | ❌ |
| Benutzerspeicher | Anwendungsspezifische Daten | ✅ |
| Reserviert | Passwörter für Zugriffs-/Kill-Befehle | ✅ (Eingeschränkt) |
Bewährte Vorgehensweise: Verwenden Sie EPC für SKU- oder Produktkennungen und den Benutzerspeicher für zusätzliche Daten wie Zeitstempel, Chargennummern oder Logistik-Metadaten.
Bit- und Blockformatierung
- Der Speicher ist in Blöcke (16 oder 32 Bit) unterteilt.
- Jeder Block kann einzeln adressiert werden.
- Die Datenkodierung muss die Blockgröße und die Tag-Spezifikationen berücksichtigen.
Beispiel: Ein Tag mit 512 Bit Benutzerspeicher verfügt über 64 Byte für die Codierung – planen Sie Ihre Datenstruktur entsprechend.
Wie sicher sind Daten auf RFID-Tags?
Da die RFID-Technologie zunehmend in Lieferketten und Konsumgüter integriert wird, ist die Datensicherheit zu einem wichtigen Thema geworden. Für eine sichere Implementierung ist es entscheidend zu verstehen, wie RFID-Tags Daten schützen – und manchmal auch offenlegen.
Können RFID-Tags gehackt werden?
Ja – aber der Kontext spielt eine Rolle. Während einfache, kostengünstige Tags geklont oder ausgelesen werden können, verfügen die meisten modernen RFID-Systeme über mehrere Sicherheitsebenen, darunter Zugriffskontrolle und Verschlüsselung.
Sicherheitsmechanismen in RFID-Tags
| Sicherheitsfunktion | Beschreibung | Schutzstufe |
|---|---|---|
| Passwortschutz | Blockiert unbefugte Lese-/Schreibvorgänge | Medium |
| Zugriffskontrollbits | Lese-/Schreibberechtigungen pro Speicherbank definieren | Hoch |
| Verschlüsselung (AES, DES) | Verwendung in Hochsicherheitsetiketten (z. B. Bankwesen, Zugangskontrolle) | Sehr hoch |
| Tötungsbefehle | Deaktivieren Sie ein Tag dauerhaft, um Missbrauch zu verhindern. | Kontextbezogen |
Häufige Schwachstellen
- Abhören: Angreifer fangen die Kommunikation zwischen Tag-Lesegerät und Tag ab.
- Klonen: Kopieren von Tag-Daten auf einen anderen Tag.
- Replay-Angriffe: Wiederverwendung von erfassten Übertragungsdaten.
Bewährte Verfahren für den sicheren Einsatz von RFID
- Verwenden Sie passwortgeschützte oder verschlüsselte Tags für kritische Daten.
- Vermeiden Sie es, sensible Informationen direkt auf Tags zu speichern – speichern Sie nur Referenzen oder IDs.
- Implementieren Sie sichere Backend-Datenbanken, um Tag-Daten zu validieren.
- Tags nach der Verwendung in sensiblen Kontexten schützen oder deaktivieren.
Wie viele Daten können RFID-Tags speichern?
Eine der häufigsten Fragen, die Ingenieure stellen, lautet:
“Wie viele Daten kann ich auf einem RFID-Tag speichern?”
Typische RFID-Speicherkapazitäten
| Tag-Typ | Speicherbereich | Anwendungsfall |
|---|---|---|
| Niedrige Frequenz (LF) | 64–256 Bit | Tier-IDs, Zugangskarten |
| Hochfrequenz (HF/NFC) | 128–4.096 Bit | Smartcards, Inventar |
| Ultrahochfrequenz (UHF) | 96–8.192 Bit | Logistik, industrielle Nachverfolgung |
| Aktives RFID | 32 KB+ | Sensordaten, große Nutzlasten |
Faktoren, die die Kapazität beeinflussen
- Tag-Häufigkeit und Chip-Modell.
- Verwendung von Verschlüsselungs- oder Prüfsummendaten.
- Anwendungstyp (z. B. EPC-Kodierung vs. benutzerdefiniert).
Welche Art von Daten werden in der Regel gespeichert?
- Produktkennungen (EPC)
- Chargen- oder Losnummern
- Zeitstempel
- Sensordaten (Temperatur, Druck) in aktiven Tags
Tipp: Speichern Sie nur die minimal notwendigen Daten auf dem Tag und verlinken Sie für Details auf externe Datenbanken. Dies reduziert den Speicherbedarf und verbessert die Leistung.
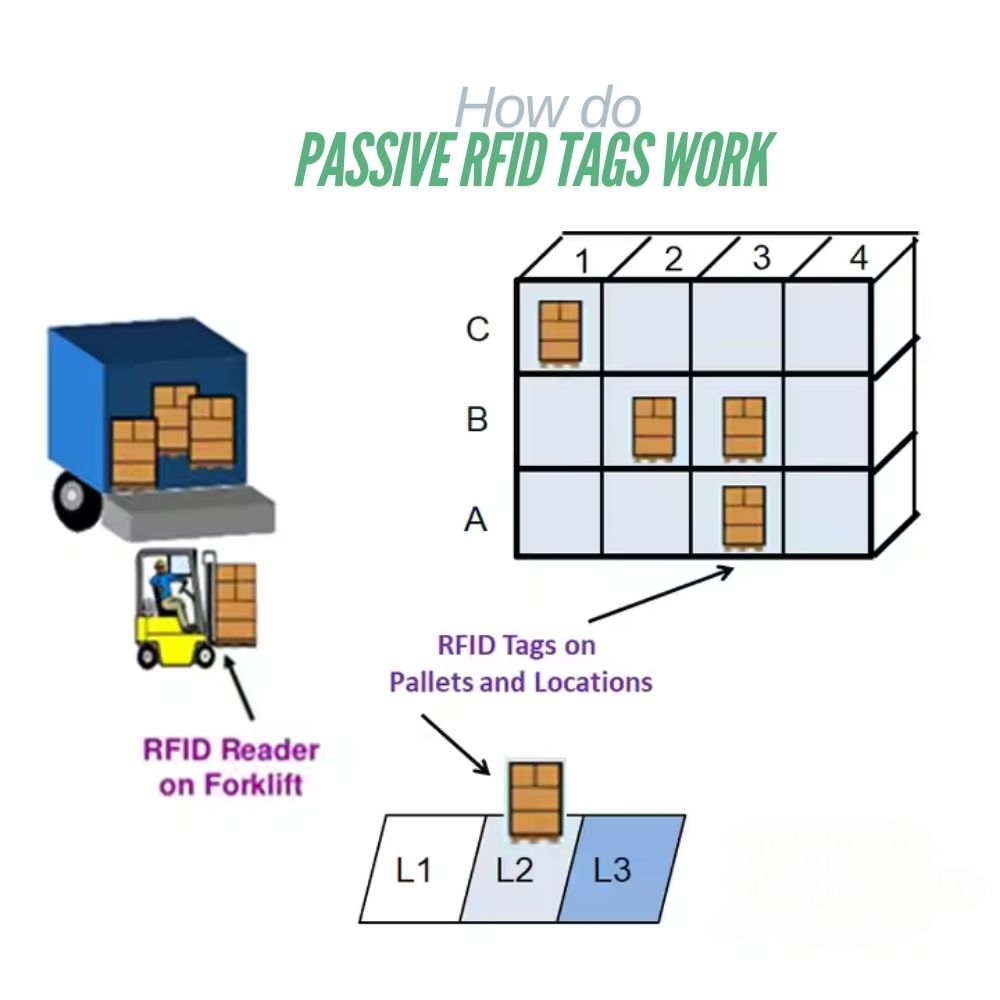
Passive vs. aktive RFID: Vergleich der Datenspeicherkapazitäten
Die Wahl zwischen passiver und aktiver RFID wirkt sich auf Kosten, Datenkapazität und Reichweite aus.
| Besonderheit | Passive RFID | Aktives RFID |
|---|---|---|
| Stromquelle | Unterstützt durch Leser | Eingebauter Akku |
| Datenkapazität | 96–8.192 Bit | 32 KB oder mehr |
| Reichweite | Bis zu 10 m | Bis zu 100 m |
| Lebensdauer | Unbegrenzt (keine Batterie) | Durch die Batterielebensdauer begrenzt |
| Kosten | <$0,10 pro Tag | $10–$50 pro Tag |
Was sollten Sie wählen?
- Passive Tags: Ideal für Inventarisierung, Einzelhandel, Zugangskontrolle.
- Aktive Tags: Am besten geeignet für die Echtzeit-Verfolgung von Vermögenswerten, Logistik und IoT-Sensoren.
Beispiele aus der Praxis – Welche Daten werden auf RFID-Tags gespeichert?
Schauen wir uns einmal an, wie die Speicherung von RFID-Daten in realen Branchen funktioniert.
Im Einzelhandel
- Produkt-ID (EPC)
- Preise, SKU und Chargennummern
- Regalplatzierung oder Kategoriedaten
Im Gesundheitswesen
- Patientenkennung
- Informationen zur Medikamentendosierung
- Geräteverfolgung
In der Logistik
- Sendungs-IDs, Zeitstempel
- Container-Codes
- Routen- und Kontrollpunktverfolgung
Bei der Tierverfolgung
- Rasse-ID, Impfpass
- GPS oder Standortkennungen (in aktiven Tags)
Pro Insight: Die meisten Unternehmenssysteme verknüpfen Tag-IDs mit Cloud-Datenbanken (ERP, WMS), wodurch die Notwendigkeit verringert wird, große Datensätze auf dem Tag selbst zu speichern.
Wie Daten auf RFID-Tags geschrieben werden (Kodierungsprozess)
Hardware-Anforderungen
- RFID-Schreibgerät oder Lese-/Schreibmodul
- Kompatible Software (TagWriter, Arduino IDE oder SDKs)
- RFID-kompatible Tags
Typischer Kodierungs-Workflow
- Verbinden Sie Ihren Writer mit dem System oder Mikrocontroller.
- Wählen Sie den Tag-Typ und die Frequenz (LF, HF, UHF).
- Wählen Sie das Datenformat (EPC, HEX oder ASCII).
- Schreiben Sie Daten mithilfe von Softwarebefehlen auf das Tag.
- Überprüfen Sie die Daten mit einer Lesefunktion.
Gängige Kodierungsformate
| Format | Beispiel | Anwendungsfall |
|---|---|---|
| EPC (96 Bit) | 300833B2DDD9014000000001 | Produkt-ID |
| HEX | 0xA1B2C3D4 | Binäre Datenspeicherung |
| ASCII | “ARTIKEL00123” | Lesbare Zeichenfolgen |
Benötigen Sie Encoder in Industriequalität? Stöbern Sie in unserem Angebot. RFID-Schreibersätze für UHF- und NFC-Systeme.
RFID vs. Barcode vs. NFC: Vergleich der Datenspeicherung
| Besonderheit | RFID | Barcode | NFC |
|---|---|---|---|
| Datenkapazität | 64 Bit – 32 KB | 12–20 Zeichen | Bis zu 4 KB |
| Lesebereich | 1–100 m | 0,2–1 m | 0-10 cm |
| Umschreibbar? | Ja | NEIN | Ja |
| Gleichzeitiges Lesen | Hunderte von Tags | Einer nach dem anderen | Einer nach dem anderen |
| Haltbarkeit | Hoch | Niedrig | Medium |
Die wichtigsten Erkenntnisse
- RFID: Am besten geeignet für Umgebungen mit hohen Geschwindigkeiten und großen Datenmengen.
- Barcode: Einfach und kostengünstig für statische IDs.
- NFC: Ideal für sichere Interaktionen über kurze Entfernungen (z. B. Zahlungen).
Denken Sie darüber nach, von Barcodes auf RFID umzusteigen? Erhalten Sie ein kostenloses Angebot für die Implementierung.
Häufig gestellte Fragen zur RFID-Datenspeicherung
Können RFID-Tags überschrieben werden?
Ja – die meisten HF- und UHF-Tags unterstützen mehrere Schreibzyklen, bis eine Abnutzung des Speichers auftritt.
Wie lange bleiben Daten auf einem RFID-Tag gespeichert?
Bis zu 10 Jahre oder mehr für passive Tags, abhängig von der Chip-Qualität.
Sind RFID-Daten verschlüsselt?
Einige Tags unterstützen AES/DES-Verschlüsselung, andere basieren auf Passwortschutz.
Kann ich RFID-Tags mit einem Smartphone programmieren?
Ja, wenn sie NFC-kompatibel sind (13,56 MHz) und Ihr Telefon über einen NFC-Leser verfügt.
Welche Software wird zum Beschreiben von RFID-Tags verwendet?
TagWriter, Arduino IDE (mit Bibliotheken) oder SDKs des Herstellers.
Die Zukunft der RFID-Datenspeicherung
Die Zukunft von RFID liegt an der Schnittstelle zwischen IoT und KI – wo Tags nicht nur Daten speichern, sondern aktiv mit Cloud-Systemen und Sensoren kommunizieren.
Aufkommende Innovationen
- Erhöhte Speicherdichte mit Mikro-EEPROM-Technologie
- Integrierte Sensoren, die Temperatur- oder Bewegungsdaten speichern
- KI-gestützte RFID-Analysen zur Automatisierung der Entscheidungsfindung
- Blockchain-gestützte Rückverfolgbarkeit für die Echtheit von Produkten
Fazit: Zusammenfassung
RFID-Tags sind kleine, aber leistungsstarke Datenträger, die die Grundlage der modernen Automatisierung bilden.
Vom Verständnis grundlegender Speicherstrukturen bis hin zu fortgeschrittener Verschlüsselung – wenn Ingenieure, Entwickler und Unternehmen wissen, wie RFID-Tags Daten speichern und übertragen, können sie intelligentere und sicherere Systeme entwickeln.
Wichtige Erkenntnisse:
- Wählen Sie die Tag-Typen basierend auf Reichweite, Kapazität und Anwendung aus.
- Verwenden Sie eine sichere, passwortgeschützte Verschlüsselung für sensible Daten.
- Integrieren Sie RFID in Backend-Systeme, um Skalierbarkeit zu gewährleisten.
Benötigen Sie Hilfe bei der Konzeption oder Programmierung Ihres RFID-Systems?
Kontakt zu unserem Team für kundenspezifische RFID-Lösungen, Hardware-Beschaffung und Implementierungsunterstützung.

Ray Zhou
Dieser Artikel wurde von Ray Zhou verfasst, einem RFID-Technologieexperten mit mehr als 10 Jahren Branchenerfahrung.
Kommentare
heiße Produkte
Niederfrequenz-RFID vs. Hochfrequenz-RFID: Die wichtigsten 14 Unterschiede
Niederfrequenz-RFID und Hochfrequenz-RFID sind beides induktive RFID-Technologien, die auf einer Magnetfeldkopplung zwischen dem
Was sind passive RFID-Tags und wie funktionieren sie?
Ein passiver RFID-Tag ist ein RFID-Tag, der keine interne Stromquelle hat. Er kann nicht laufen oder übertragen durch

13,56-MHz-RFID-Karten und -Tags erklärt: Alles, was Sie wissen sollten
Die RFID-Technologie spielt eine wichtige Rolle in modernen Identifizierungs- und Datenaustauschsystemen. Unter den verschiedenen RFID-Frequenzen ist 13,56 MHz
RFID in der Logistik: Wie man RFID-Fehlleitungen und RFID-Etikettenfehler beseitigt
RFID in der Logistik ist mehr als nur ein Werkzeug zur Beschleunigung von Prozessen. Es ist zu einem wesentlichen Bestandteil der Funktionsweise moderner Lieferketten geworden.
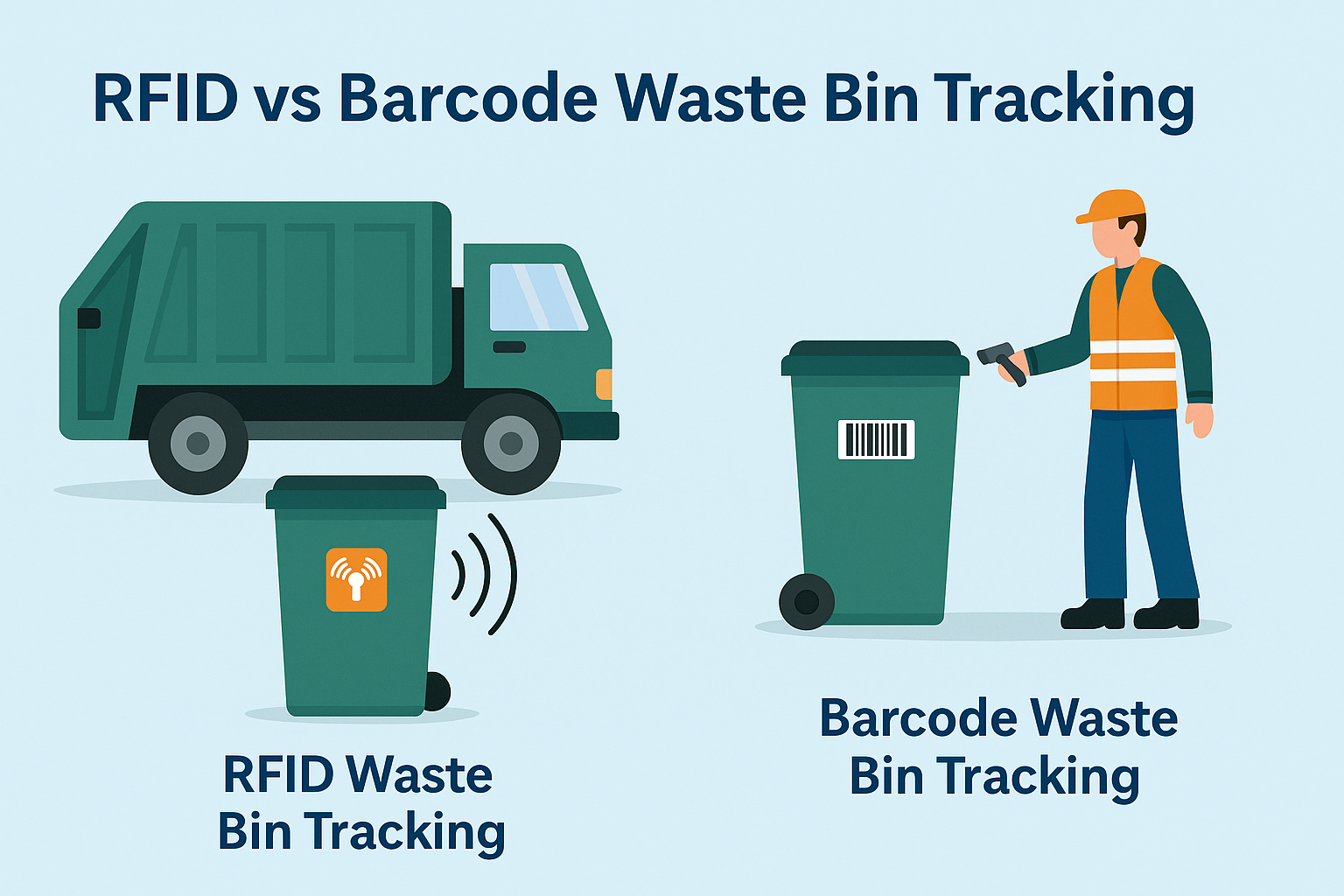
Was ist RFID-Abfallmanagement?
Stellen Sie sich eine Stadt vor, in der jeder Mülleimer spricht – nicht im wörtlichen Sinne, sondern über einen winzigen Chip, der dem System mitteilt, wann er voll ist, wann er geleert wurde und wohin er gebracht wurde. Genau das leistet heute die RFID-Abfallwirtschaft.

Was sind Schraubendichtungen und ihre Anwendungen? | Vollständiger Leitfaden
Im globalen Handel und in der Logistik spielen Bolzenplomben eine entscheidende Rolle bei der Gewährleistung der Frachtsicherheit und der Einhaltung von Vorschriften. Diese kleinen, aber leistungsstarken Geräte sind so konzipiert, dass sie Schiffscontainer, Anhänger und Frachttüren mit einem manipulationssicheren Mechanismus verriegeln.
Schlagwörter
VERWANDTE BLOGS
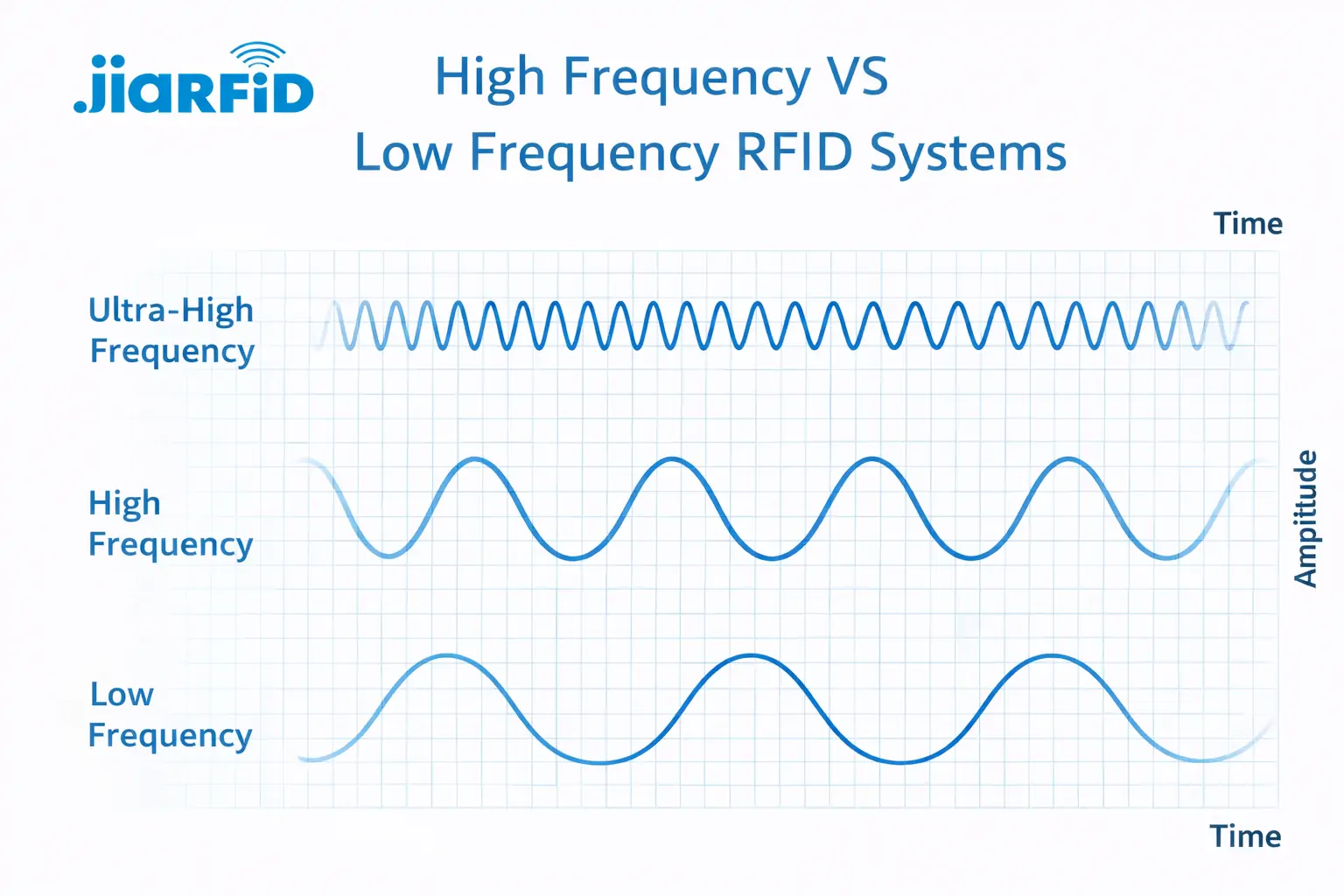
Niederfrequenz-RFID vs. Hochfrequenz-RFID: Die wichtigsten 14 Unterschiede
Niederfrequenz-RFID und Hochfrequenz-RFID sind beides induktive RFID-Technologien, die auf einer Magnetfeldkopplung zwischen dem
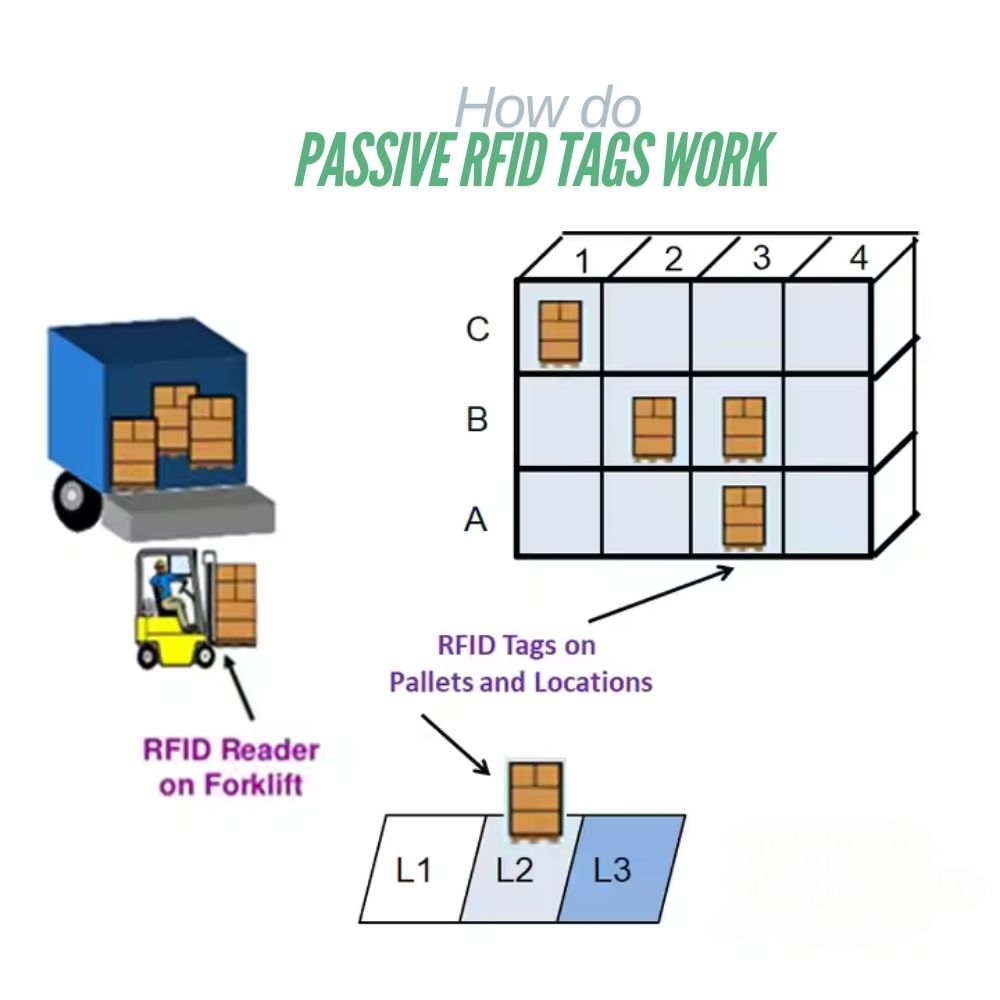
Was sind passive RFID-Tags und wie funktionieren sie?
Ein passiver RFID-Tag ist ein RFID-Tag, der keine interne Stromquelle hat. Er kann nicht laufen oder übertragen durch

13,56-MHz-RFID-Karten und -Tags erklärt: Alles, was Sie wissen sollten
Die RFID-Technologie spielt eine wichtige Rolle in modernen Identifizierungs- und Datenaustauschsystemen. Unter den verschiedenen RFID-Frequenzen ist 13,56 MHz




