
Hvordan gemmer RFID-tags data?
Indholdsfortegnelse
Indledning
At forstå denne proces er ikke kun akademisk. For ingeniører, der designer intelligente forsyningskæder, udviklere, der bygger RFID-integrerede apps, og IT-ledere, der overvåger sporing af aktiver i stor skala, er de underliggende mekanismer i RFID-hukommelse, datakodning og sikkerhedsprotokoller afgørende for ydeevne, interoperabilitet og dataintegritet.
Hvad er RFID, og hvordan virker det?
Hvad er RFID?
RFID (Radio Frequency Identification) er en trådløs teknologi, der automatisk identificerer og sporer objekter ved hjælp af elektromagnetiske felter. I modsætning til stregkoder kræver RFID ikke direkte synsfelt og kan gemme flere data direkte på mærket.
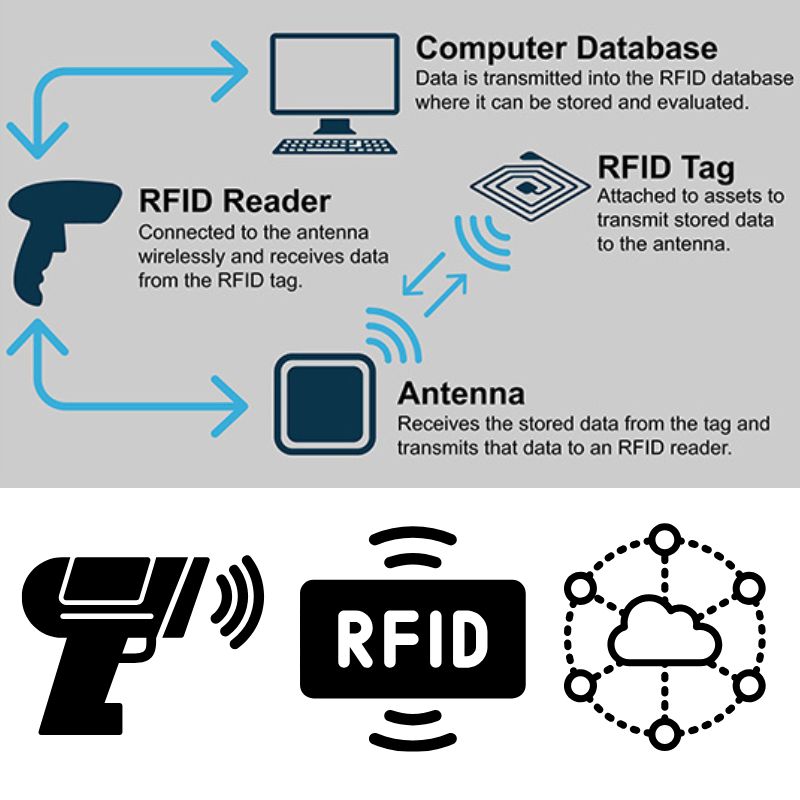
Nøglekomponenter i et RFID-system
- RFID tag (Transponder): En chip og antenne indbygget i en etiket eller et objekt, der lagrer data.
- RFID-læser (Interrogator): Sender et radiosignal for at aktivere mærket og modtage dets data.
- Middleware/systemsoftware: Behandler, gemmer og videresender data til databaser eller applikationer.
Sådan fungerer datatransmission
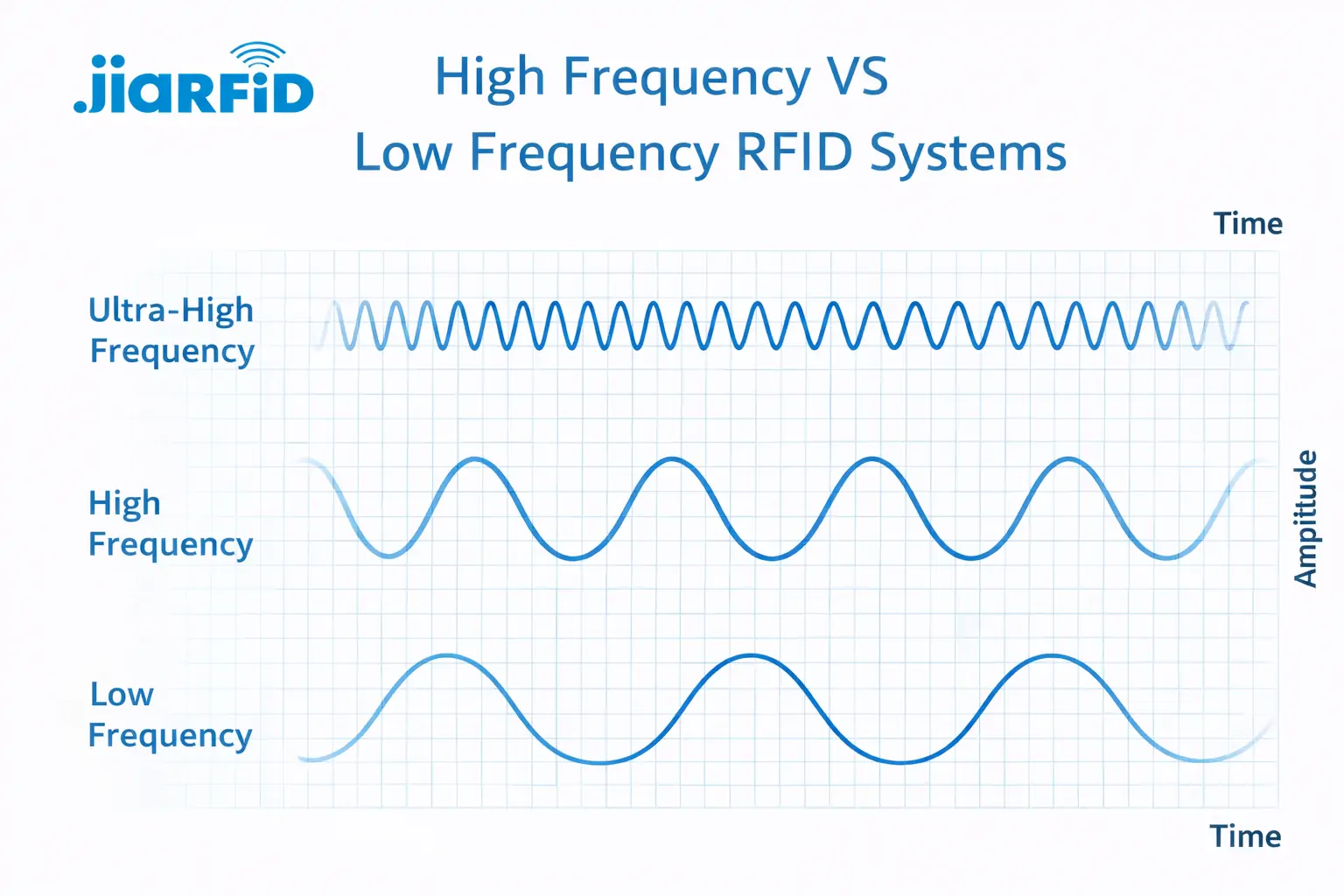
Når RFID-læseren udsender et radiofrekvenssignal, opfanger tagets antenne det og forsyner chippen med strøm (hvis den er passiv). Chippen modulerer derefter og sender de lagrede data tilbage til læseren. Denne kommunikation varierer afhængigt af frekvensen:
- LF (lav frekvens): Kort rækkevidde, velegnet til sporing af dyr.
- HF (højfrekvens): Almindelig i NFC og smartkort.
- UHF (Ultra High Frequency): Længere rækkevidde, hurtigere læsehastigheder – ideel til logistik.
Teknisk tip: Passive UHF-tags bruges oftest i industrielle forsyningskæder, fordi de er billige og kan transmittere op til flere meter.
Begyndervejledning til programmering af RFID-tags
Programmering af RFID-tags kan frigøre kraftfulde muligheder – fra tilpasning af produktdata til sikker adgangskontrol. Der findes mange værktøjer og tilgange, men den specifikke metode afhænger af tagtypen, frekvensen og anvendelsen.
Vi arbejder i øjeblikket på verificerede kodeeksempler og praktiske vejledninger til sikker og effektiv programmering af RFID-tags. Dette afsnit vil snart indeholde:
- Praktiske vejledninger til brug af Arduino med RFID-moduler.
- Kodning af data ved hjælp af TagWriter (Android) til NFC-kompatible tags.
- Brug af RFID SDK'er og desktop-skrivere til virksomhedsapplikationer.
- Tips til valg af det rigtige hukommelsesformat (ASCII, HEX, EPC).
Vil du starte nu? Vi anbefaler, at du i mellemtiden udforsker disse ressourcer:
- NXP TagWriter-app– NFC-kodning til Android
- MFRC522 Arduino-bibliotek på GitHub– Open source RFID-læserbibliotek
- [Din hardwareleverandørs SDK eller udviklerværktøjer] til specifikke læsermodeller
Brug for hjælp til at skrive data til dine RFID-tags eller vælge kompatible værktøjer? Kontakt vores tekniske team for personlig support.
Hvordan RFID-tags gemmer data internt
I sin kerne er et RFID-tag en lille lagerenhed med specifikke hukommelsesbanker. Det er afgørende at forstå det interne hukommelseslayout, når man planlægger, hvilken type data der skal lagres – og hvor meget.
Typer af hukommelse i RFID-tags
- ROM (Read-Only Memory): Data skrevet under fremstillingen. Kan ikke ændres.
- EEPROM (Electrically Erasable): Omskrivbar; mest almindeligt anvendt i moderne RFID.
- RAM: Midlertidig lagerplads, der ofte bruges under aktive transaktioner.
Almindelige hukommelsestyper
- Skrivebeskyttet (RO): Kan ikke ændres. Anvendes til faste ID'er.
- Læs/skriv (RW): Kan ændres med kompatible læsere.
- WORM (Write Once, Read Many): Når dataene er programmeret, låses de.
Hukommelsesbanker i EPCglobal Gen2-tags (UHF)
| Hukommelsesbank | Indhold | Skrivbar? |
|---|---|---|
| EPC | Produkt-ID (typisk 96-128 bits) | ✅ |
| TID | Unik tag/chip-identifikator | ❌ |
| Brugerhukommelse | Applikationsspecifikke data | ✅ |
| Reserveret | Adgangskoder til adgang/kill-kommandoer | ✅ (Begrænset) |
Bedste praksis: Brug EPC til SKU- eller produktidentifikatorer og brugerhukommelse til ekstra data såsom tidsstempler, batchnumre eller logistikmetadata.
Bit- og blokformatering
- Hukommelsen er opdelt i blokke (16 eller 32 bits).
- Hver blok kan adresseres individuelt.
- Datakodning skal overholde blokstørrelse og tag-specifikationer.
Eksempel: Et tag med 512 bit brugerhukommelse har 64 byte til rådighed til kodning – planlæg din datastruktur i overensstemmelse hermed.
Hvor sikre er data på RFID-tags?
I takt med at RFID-teknologien bliver mere integreret i forsyningskæder og forbrugerprodukter, er datasikkerhed blevet et vigtigt emne. For at sikre en sikker implementering er det afgørende at forstå, hvordan RFID-tags beskytter – og undertiden afslører – data.
Kan RFID-tags hackes?
Ja — men konteksten er vigtig. Mens enkle lavpris-tags kan klones eller skimmes, implementerer de fleste moderne RFID-systemer flere sikkerhedslag, herunder adgangskontrol og kryptering.
Sikkerhedsmekanismer i RFID-tags
| Sikkerhedsfunktion | Beskrivelse | Beskyttelsesniveau |
|---|---|---|
| Adgangskodebeskyttelse | Blokerer uautoriserede læsninger/skrivninger | Medium |
| Adgangskontrolbits | Definer læse-/skriveadgang pr. hukommelsesbank | Høj |
| Kryptering (AES, DES) | Anvendes i høj sikkerhedsmærker (f.eks. bank, adgangskontrol) | Meget høj |
| Dræb kommandoer | Deaktiver et tag permanent for at forhindre misbrug | Kontekstuel |
Almindelige sårbarheder
- Aflytning: Angribere opfanger kommunikationen mellem tag-læser og server.
- Kloning: Kopiering af tagdata til et andet tag.
- Replay-angreb: Genbrug af indsamlede transmissionsdata.
Bedste praksis for sikker RFID-implementering
- Brug adgangskodebeskyttede eller krypterede tags til kritiske data.
- Undgå at gemme følsomme oplysninger direkte på tags — gem kun referencer eller ID'er.
- Implementer sikre backend-databaser til validering af tagdata.
- Skjult eller deaktiver tags efter brug i følsomme sammenhænge.
Hvor meget data kan RFID-tags gemme?
Et af de mest almindelige spørgsmål, som ingeniører stiller, er:
“Hvor meget data kan jeg gemme på et RFID-tag?”
Typiske RFID-hukommelseskapaciteter
| Tag Type | Hukommelsesområde | Use Case |
|---|---|---|
| Lav frekvens (LF) | 64–256 bits | Dyre-ID'er, adgangskort |
| Højfrekvens (HF/NFC) | 128–4.096 bits | Smartkort, lagerbeholdning |
| Ultrahøj frekvens (UHF) | 96–8.192 bits | Logistik, industriel sporing |
| Aktiv RFID | 32 KB+ | Sensordata, store nyttelaster |
Faktorer, der påvirker kapaciteten
- Tagfrekvens og chipmodel.
- Brug af kryptering eller kontrolsumdata.
- Applikationstype (f.eks. EPC-kodning vs. brugerdefineret).
Hvilken type data gemmes typisk?
- Produktidentifikatorer (EPC)
- Batch- eller partinummer
- Tidskoder
- Sensordata (temperatur, tryk) i aktive tags
Tip: Gem kun de minimale data, der er nødvendige på tagget, og link til eksterne databaser for detaljer. Dette reducerer hukommelseskravene og forbedrer ydeevnen.
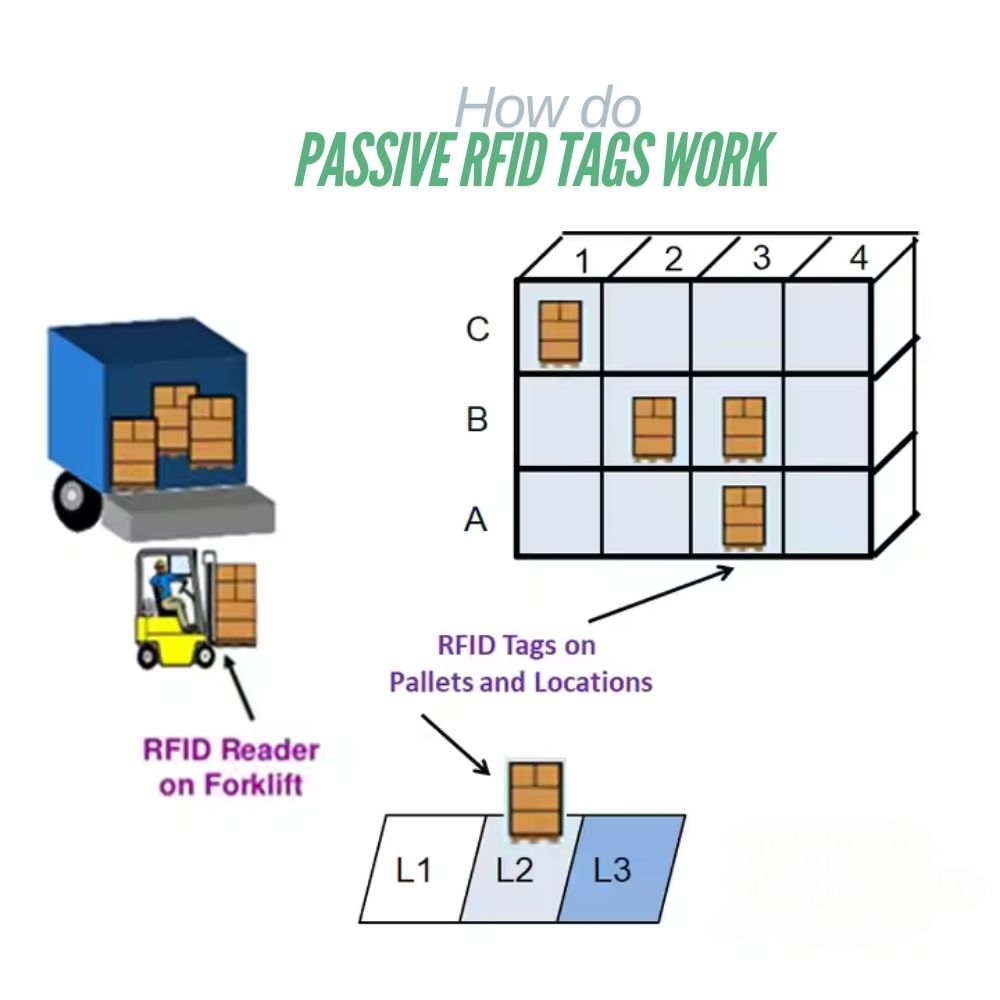
Passiv vs. aktiv RFID: Sammenligning af datalagringskapacitet
Valget mellem passiv og aktiv RFID har indflydelse på omkostninger, datakapacitet og rækkevidde.
| Feature | Passiv RFID | Aktiv RFID |
|---|---|---|
| Strømkilde | Drevet af læser | Indbygget batteri |
| Datakapacitet | 96–8.192 bits | 32 KB eller mere |
| Rækkevidde | Op til 10 m | Op til 100 m |
| Levetid | Ubegrænset (ingen batteri) | Begrænset af batteriets levetid |
| Koste | <$0,10 pr. tag | $10–$50 pr. tag |
Hvilken skal du vælge?
- Passive tags: Ideelle til lagerstyring, detailhandel og adgangskontrol.
- Aktive tags: Bedst til sporing af aktiver i realtid, logistik, IoT-sensorer.
Eksempler fra virkeligheden — Hvilke data gemmes på RFID-tags?
Lad os se på, hvordan RFID-datalagring fungerer i virkelige brancher.
I detailhandlen
- Produkt-ID (EPC)
- Priser, SKU og partinummer
- Hyldeplacering eller kategoridata
I sundhedsvæsenet
- Patient-ID
- Oplysninger om medicindosering
- Udstyrssporing
I logistik
- Forsendelses-ID'er, tidsstempler
- Containerkoder
- Rute- og kontrolpunktssporing
I dyresporing
- Race-ID, vaccinationsjournaler
- GPS eller placeringsidentifikatorer (i aktive tags)
Pro Insight: De fleste virksomhedssystemer knytter tag-id'er til cloud-databaser (ERP, WMS), hvilket reducerer behovet for at gemme store datasæt på selve tagget.
Hvordan data skrives til RFID-tags (kodningsproces)
Hardwarekrav
- RFID-skriver eller læser/skriver-modul
- Kompatibel software (TagWriter, Arduino IDE eller SDK'er)
- RFID-kompatible tags
Typisk kodningsworkflow
- Tilslut din printer til systemet eller mikrocontrolleren.
- Vælg tagtype og frekvens (LF, HF, UHF).
- Vælg dataformat (EPC, HEX eller ASCII).
- Skriv data til tagget ved hjælp af softwarekommandoer.
- Bekræft data ved hjælp af en læsefunktion.
Almindelige kodningsformater
| Format | Eksempel | Use Case |
|---|---|---|
| EPC (96-bit) | 300833B2DDD9014000000001 | Produkt-ID |
| HEX | 0xA1B2C3D4 | Binær datalagring |
| ASCII | “ITEM00123” | Læselige strenge |
Har du brug for encodere i industriel kvalitet? Se vores udvalg RFID-skriver-sæt til UHF- og NFC-systemer.
RFID vs. stregkode vs. NFC: Sammenligning af datalagring
| Feature | RFID | Stregkode | NFC |
|---|---|---|---|
| Datakapacitet | 64 bit – 32 KB | 12–20 tegn | Op til 4 KB |
| Læs Range | 1–100 m | 0,2–1 m | 0-10 cm |
| Kan den omskrives? | Ja | Ingen | Ja |
| Samtidige læsninger | 100'er af tags | En ad gangen | En ad gangen |
| Holdbarhed | Høj | Lav | Medium |
Nøgle takeaways
- RFID: Bedst til datamiljøer med høj hastighed og store datamængder.
- Stregkode: Enkel og billig til statiske ID'er.
- NFC: Ideel til sikre interaktioner på kort afstand (f.eks. betalinger).
Overvejer du at opgradere fra stregkoder til RFID? Få et gratis tilbud på implementering.
Ofte stillede spørgsmål om RFID-datalagring
Kan RFID-tags omskrives?
Ja — de fleste HF- og UHF-tags understøtter flere skrivecyklusser, indtil der opstår hukommelsesslid.
Hvor længe forbliver data på et RFID-mærke?
Op til 10 år eller mere for passive tags, afhængigt af chipkvaliteten.
Er RFID-data krypteret?
Nogle tags understøtter AES/DES-kryptering, mens andre er baseret på adgangskodebeskyttelse.
Kan jeg programmere RFID-tags med en smartphone?
Ja, hvis de er NFC-kompatible (13,56 MHz) og din telefon har en NFC-læser.
Hvilken software bruges til at skrive til RFID-tags?
TagWriter, Arduino IDE (med biblioteker) eller producentens SDK'er.
Fremtiden for RFID-datalagring
RFID's fremtid ligger i krydsfeltet mellem IoT og AI — hvor tags ikke kun lagrer data, men også kommunikerer aktivt med cloud-systemer og sensorer.
Nye innovationer
- Øget hukommelsestæthed med mikro-EEPROM-teknologi
- Integrerede sensorer, der gemmer temperatur- eller bevægelsesdata
- AI-drevet RFID-analyse til automatisering af beslutningstagning
- Blockchain-baseret sporbarhed for produktets ægthed
Konklusion: Sammenfatning
RFID-tags er små, men kraftfulde databærere, der udgør grundlaget for moderne automatisering.
Fra grundlæggende hukommelsesstrukturer til avanceret kryptering giver forståelsen af, hvordan RFID-tags gemmer og overfører data, ingeniører, udviklere og virksomheder mulighed for at opbygge smartere og mere sikre systemer.
Vigtigste pointer:
- Vælg tagtyper baseret på rækkevidde, kapacitet og anvendelse.
- Brug sikker, adgangskodebeskyttet kodning til følsomme data.
- Integrer RFID med backend-systemer for skalerbarhed.
Brug for hjælp til at designe eller programmere dit RFID-system?
Kontakt vores team til skræddersyede RFID-løsninger, hardware-sourcing og implementeringssupport.

Ray Zhou
Denne artikel er skrevet af Ray Zhou, en ekspert i RFID-teknologi med mere end 10 års brancheerfaring.
Kommentarer
Hotte produkter

Kan iPhone læse RFID?
Ja, men ikke alle RFID-tags. En iPhone kan i visse tilfælde læse RFID via sin NFC-funktion, som gør det muligt at

RFID-styringssystem til vasketøj - den komplette guide
RFID ændrer den måde, hvorpå moderne vaskerier håndterer tekstilaktiver. I stedet for at behandle sengetøj, uniformer, håndklæder eller beklædningsgenstande som bulk

Hvad er en RFID-læser? Hvordan fungerer den, hvilke typer findes der, og hvordan vælger man en?
RFID-teknologi bruges i mange hverdagssystemer, lige fra lagersporing og adgangskontrol til identifikation af husdyr og forvaltning af aktiver.
Lavfrekvent RFID vs. højfrekvent RFID: De vigtigste 14 forskelle
Lavfrekvens-RFID og højfrekvens-RFID er begge induktive RFID-teknologier, der er afhængige af magnetfeltkobling mellem
Hvad er passive RFID-tags, og hvordan fungerer de?
Et passivt RFID-tag er et RFID-tag, der ikke har nogen intern strømkilde. Det kan ikke køre eller sende ved hjælp af

13,56 MHz RFID-kort og -tags forklaret: Alt hvad du bør vide
RFID-teknologien spiller en vigtig rolle i moderne identifikations- og dataudvekslingssystemer. Blandt de forskellige RFID-frekvenser er 13,56 MHz
Tags
RELATEREDE BLOGS

Kan iPhone læse RFID?
Ja, men ikke alle RFID-tags. En iPhone kan i visse tilfælde læse RFID via sin NFC-funktion, som gør det muligt at

RFID-styringssystem til vasketøj - den komplette guide
RFID ændrer den måde, hvorpå moderne vaskerier håndterer tekstilaktiver. I stedet for at behandle sengetøj, uniformer, håndklæder eller beklædningsgenstande som bulk

Hvad er en RFID-læser? Hvordan fungerer den, hvilke typer findes der, og hvordan vælger man en?
RFID-teknologi bruges i mange hverdagssystemer, lige fra lagersporing og adgangskontrol til identifikation af husdyr og forvaltning af aktiver.




