
How to Copy RFID Key Fobs and Access Cards
Table of Contents
How to Copy RFID Key Fobs and Access Cards: A Complete Guide
But what if you lose your RFID key fobs or need an extra copy for family or staff? This guide explains how copying works, which chips can be duplicated, and what legal and security precautions to follow.
Quick Checklist: How Copying Works
Before diving in, here’s a simple 4-step summary you can follow:
Scan → Write → Test → Register
- Scan your original RFID key fobs using a compatible USB RFID copier.
- Write the stored data to a blank RFID tag or card.
- Test the new tag on your door or reader.
- Register it with your system administrator if needed.
⚠️ Note: Only copy RFID key fobs or Access Cards that you own or are authorized to duplicate. Unauthorized duplication may be illegal and compromise system security.
What Is an RFID Key Fob and How Does It Work?
An RFID key fob is a small wireless device that uses Radio Frequency Identification (RFID) to communicate with a reader. When tapped on a reader, it transmits a unique ID number that the access system recognizes and grants entry.
Core Features
- Convenience: Tap-and-go entry without keys.
- Durability: Withstands daily use.
- Customizable Access: Programmed for specific users or areas.
These fobs and RFID Cards are used in apartments, offices, parking systems, and schools.
Why Copy RFID Key Fobs or Access Cards?
- Convenience: Give family members or staff their own fobs.
- Backup: Avoid lockouts if the original is lost.
- Shared Access: Simplify entry for cleaning staff, guests, or short-term rentals.
Having a backup RFID Card ensures access continuity without waiting for replacements.
Understanding Chip Types and Copy Difficulty
Not all RFID key fobs can be cloned. Copying depends on the frequency and chip type inside the card or fob.
1. 125 kHz Low Frequency (LF) – EM4100 / HID Prox
- Common use: older building systems.
- Copying: relatively easy with a basic USB RFID copier and blank 125 kHz tags.
- Process: scan → write → test → register.
2. 13.56 MHz High Frequency (HF) – MIFARE Classic
- Common use: offices, schools, transport cards.
- Copying: possible only if encryption is weak or absent.
- Tools: an advanced copier that supports MIFARE Classic.
3. DESFire / HID iCLASS / SEOS (Encrypted Smart Cards)
- Common use: enterprise or government systems.
- Copying: typically not possible without admin credentials.
- Best practice: Request an official duplicate from your building manager.
Tip: Check the frequency label on your RFID Card or scan it with an RFID reader to identify chip type before attempting duplication.

Tools You’ll Need
To copy an RFID key fob or card correctly, prepare the following:
- RFID copier or duplicator – to read and write data.
- Blank RFID tags or cards – to create new copies.
- Original RFID key fob – the source credential.
- (Optional) NFC smartphone app – limited use for some 13.56 MHz tags.
You can browse Blank 125 kHz RFID Tags and RFID Cards for Access Control from reliable suppliers.
Can I Copy an RFID Key Fob with My Phone?
Some NFC-enabled smartphones can read and emulate 13.56 MHz RFID Cards, but they can’t clone encrypted fobs.
- Works with: unprotected MIFARE Classic or NTAG chips.
- Does not work with: HID iCLASS, SEOS, or DESFire.
- Extra hardware: may be required for writing to physical cards.
Security Risks and How to Stay Safe
Copying RFID key fobs without oversight can create security issues:
- Unauthorized access: duplicates could be misused.
- Unencrypted data: Older fobs are easier to clone.
- Data theft: insecure readers might leak information.
Best practices: - Use encrypted or secure RFID Cards.
- Rotate access credentials regularly.
- Monitor entry logs for unusual patterns.
Enhancing Access Control Security
To strengthen your system:
- Upgrade to encrypted fobs (MIFARE DESFire or HID iCLASS).
- Enable two-factor access: combine RFID with PIN or biometrics.
- Track user activity: use software logs to detect anomalies.
“A properly encrypted RFID key fob reduces cloning risk and protects your entire facility.”
RFID vs. NFC: Quick Comparison
| Feature | RFID | NFC |
|---|---|---|
| Range | Up to several meters | A few centimeters |
| Typical use | Access control, logistics | Mobile payments, smartcards |
| Duplication difficulty | Moderate to high | Very high (due to encryption) |
Both use radio frequency, but NFC is more secure and typically used for smartphones and payment systems, while RFID key fobs are optimized for door entry and identification.
Encryption in Modern RFID Cards
Encryption protects the communication between the RFID card and reader, making unauthorized copying nearly impossible.
Benefits:
- Prevents data duplication.
- Preserves data integrity.
- Future-proofs your system against attacks.
Switching to encrypted RFID Cards is one of the easiest ways to prevent unauthorized copies.
FAQs About RFID Key Fobs and Access Cards
How can I tell if my key fob is encrypted?
Encrypted fobs usually require proprietary software or special readers. If a basic copier can’t read it, it’s likely encrypted.
Can I copy an RFID key fob at home?
Yes, you can with a compatible RFID copier and blank tags, but only if you have permission to duplicate them.
What’s the difference between RFID and NFC?
RFID has a longer range and multiple frequency bands; NFC is short-range and used mainly in smartphones.
Is it legal to copy an RFID access card?
Copying without authorization can violate privacy or property rules. Always get approval from the system owner.
What are the common frequencies?
125 kHz (LF) and 13.56 MHz (HF) are most common for key fobs and access cards.
Conclusion
RFID key fobs and Access Cards are powerful tools for security and convenience — but duplicating them requires understanding of chip types, tools, and legal limits.
When in doubt, seek help from a certified RFID technician or request an official replacement from your building management.
Need reliable RFID key fobs, access cards, or copiers for your project?
Talk to our RFID experts for samples, pricing, or technical advice.
📩 Email us at [email protected]

Ray Zhou
This article was written by Ray Zhou, an RFID technology expert with more than 10 years of industry experience.
Comments
Hot Products
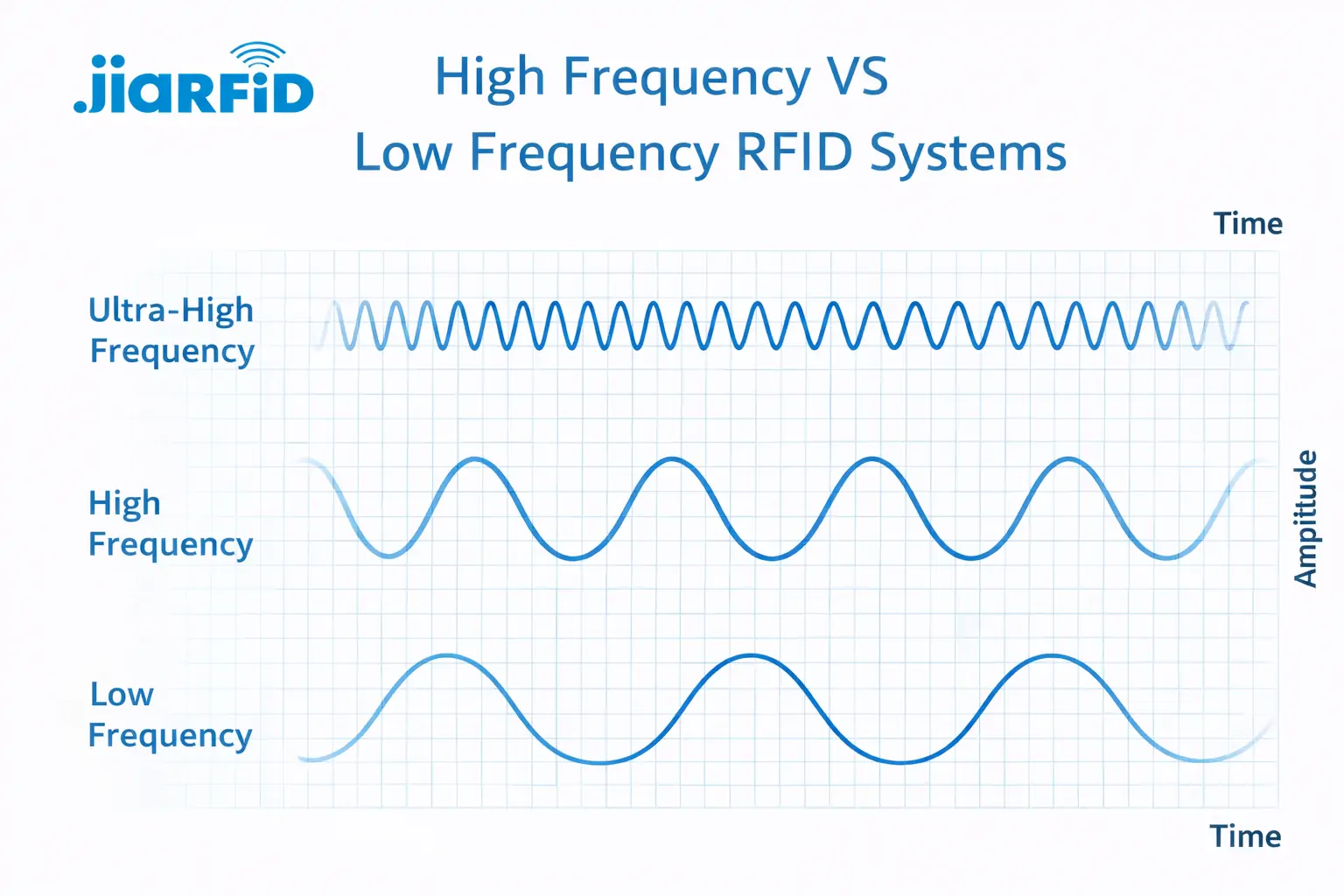
Low Frequency RFID vs. High Frequency RFID: The Major 14 Differences
Low Frequency RFID and High Frequency RFID are both inductive RFID technologies that rely on magnetic field coupling between the
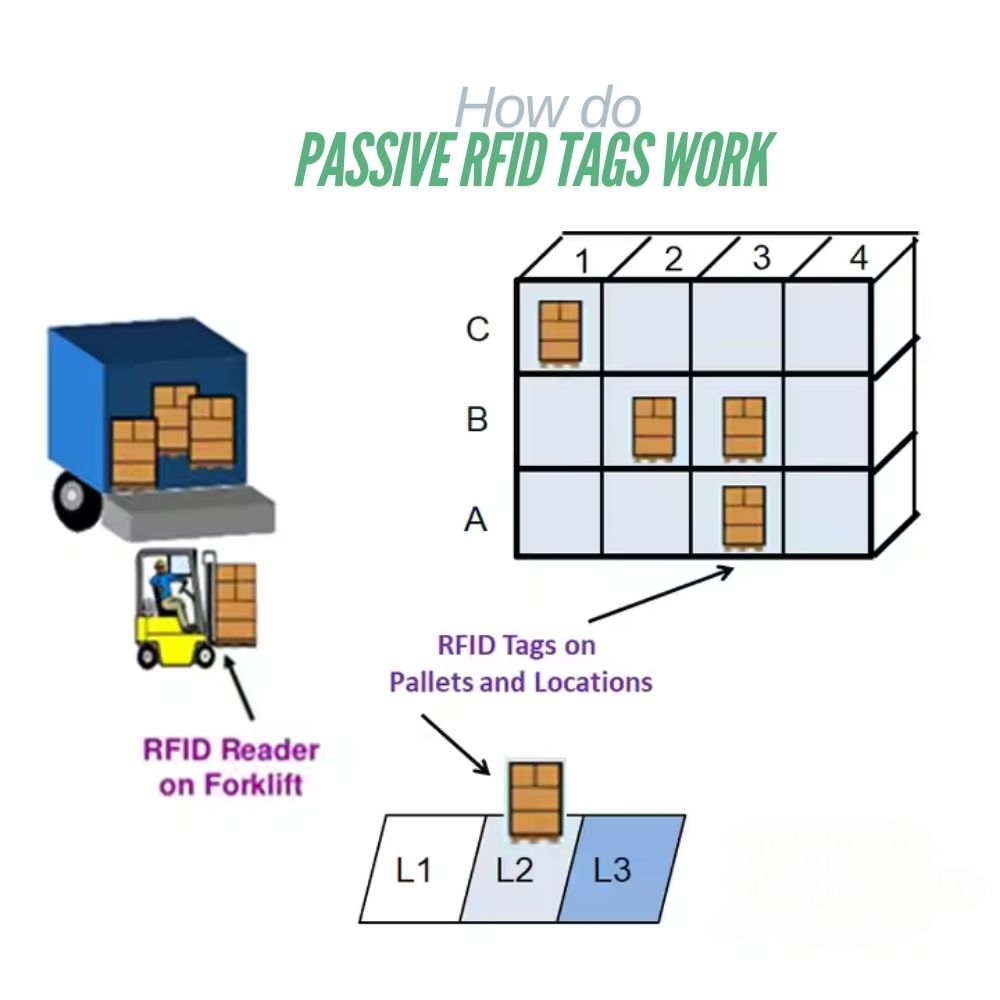
What Are Passive RFID Tags and How Do They Work
A passive RFID tag is an RFID tag that has no internal power source. It cannot run or transmit by

13.56 MHz RFID Cards and Tags Explained: Everything You Should Know
RFID technology plays an important role in modern identification and data exchange systems. Among the different RFID frequencies, 13.56 MHz
RFID in Logistics: How to Eliminate RFID Misrouting and RFID Label Failures
RFID in logistics is more than just a tool to speed up processes. It has become a key part of how modern supply chains operate.
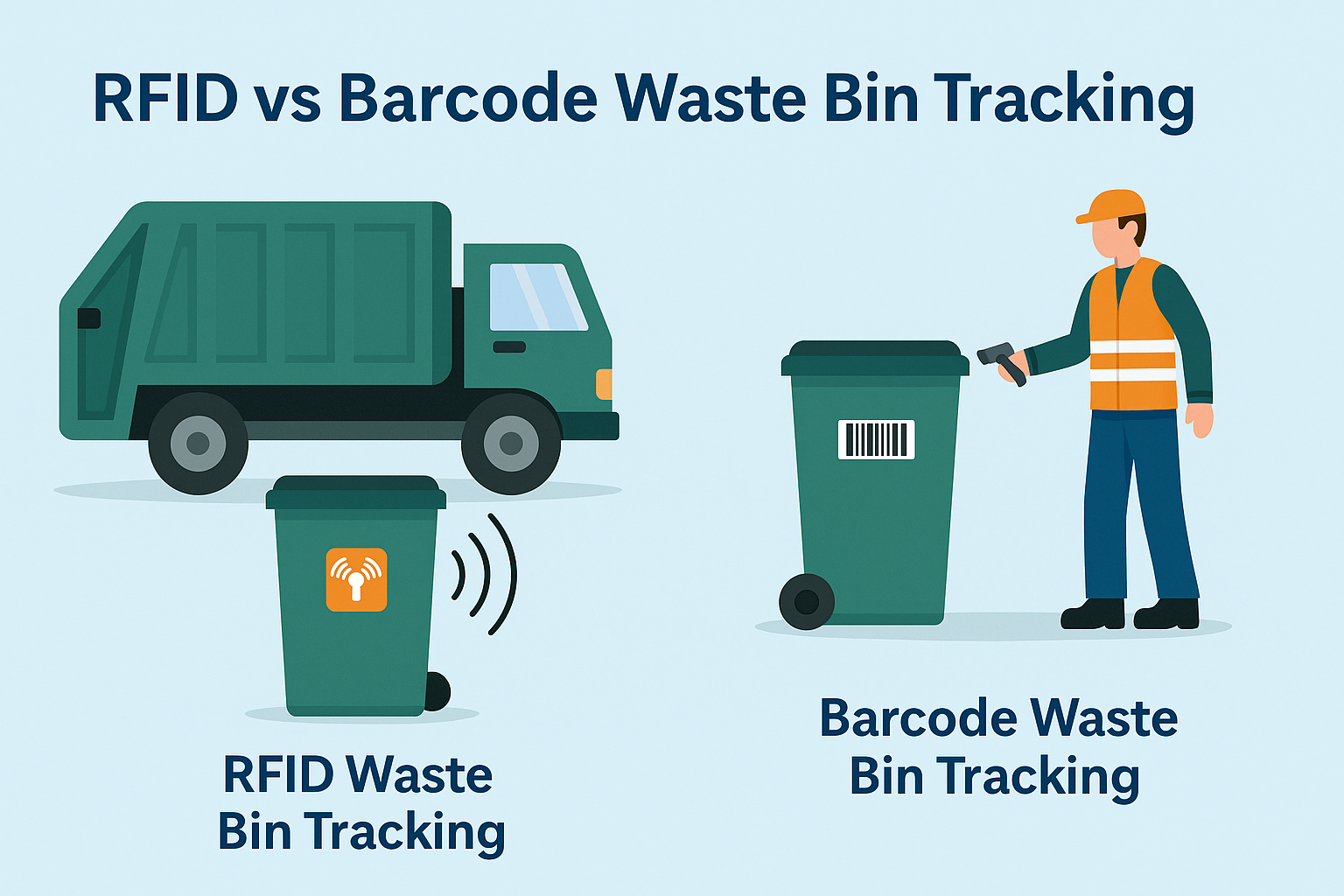
What Is RFID Waste Management
Imagine a city where every trash bin speaks — not literally — but through a tiny chip that tells the system when it’s full, when it’s emptied, and where it went. That’s what RFID waste management is doing today.

What are Bolt Seals and their Applications? | Complete Guide
In global trade and logistics, bolt seals play a crucial role in ensuring cargo security and compliance. These small but powerful devices are designed to lock shipping containers, trailers, and cargo doors with a tamper-evident mechanism.
Tags
RELATED BLOGS
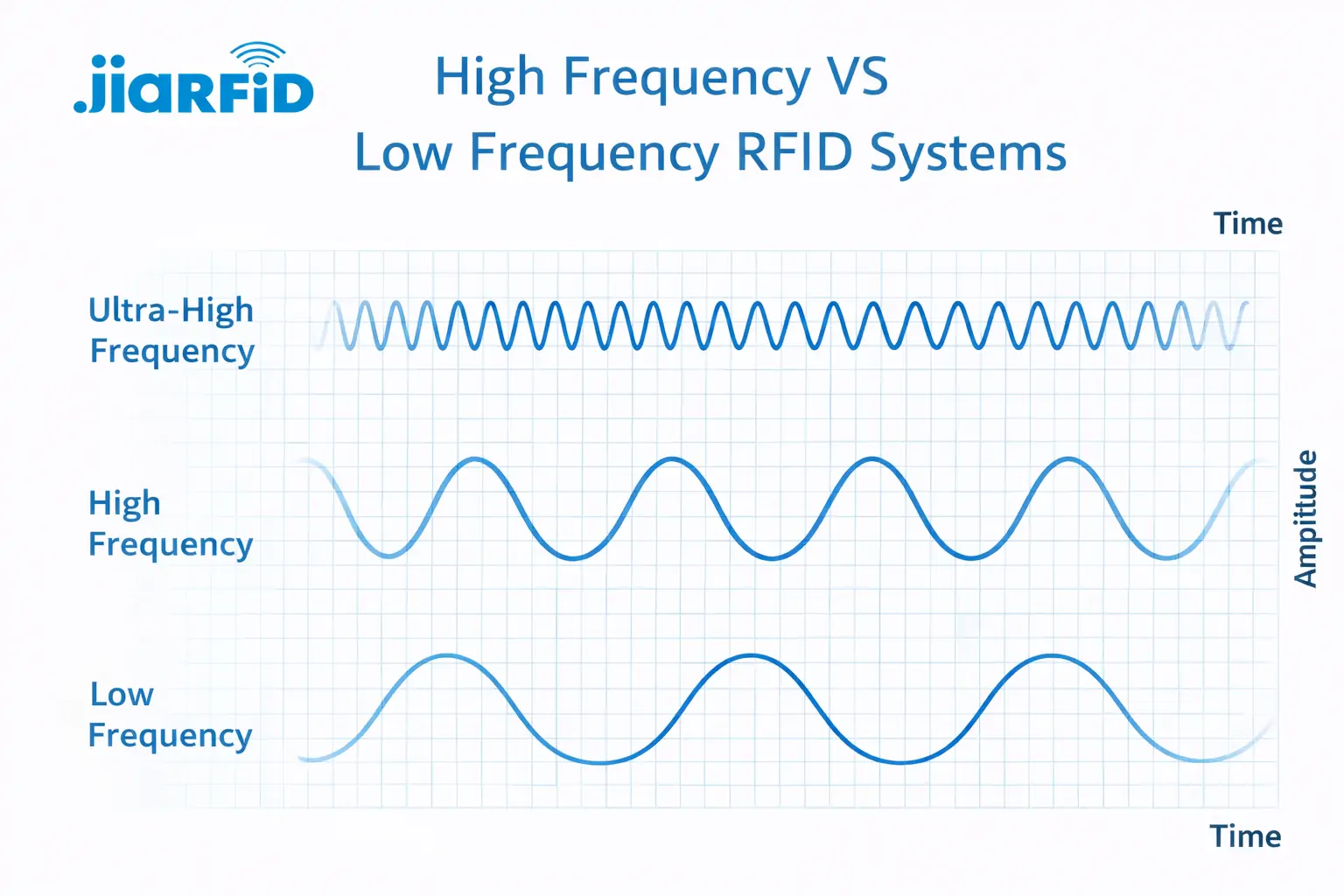
Low Frequency RFID vs. High Frequency RFID: The Major 14 Differences
Low Frequency RFID and High Frequency RFID are both inductive RFID technologies that rely on magnetic field coupling between the
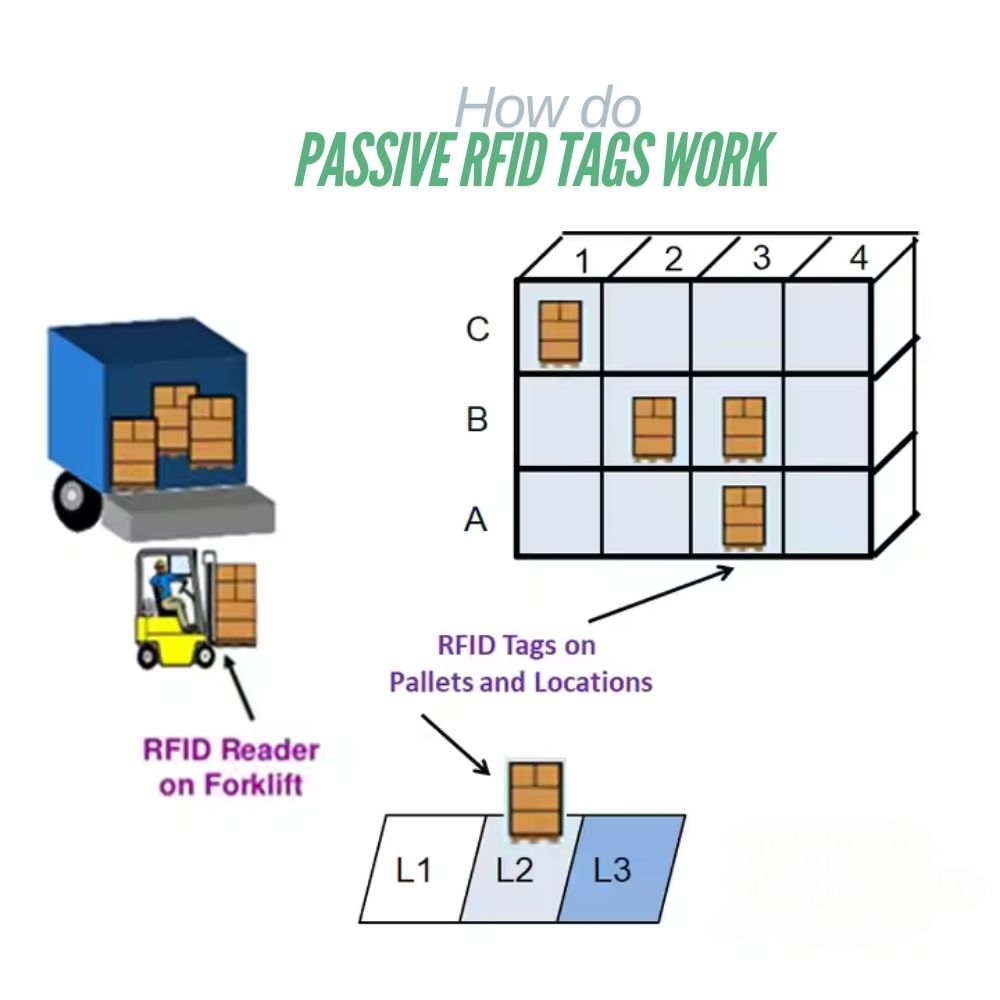
What Are Passive RFID Tags and How Do They Work
A passive RFID tag is an RFID tag that has no internal power source. It cannot run or transmit by

13.56 MHz RFID Cards and Tags Explained: Everything You Should Know
RFID technology plays an important role in modern identification and data exchange systems. Among the different RFID frequencies, 13.56 MHz




