Технология RFID играет важную роль в современных системах идентификации и обмена данными. Среди различных частот RFID 13,56 МГц является одной из наиболее распространенных, поскольку обеспечивает хороший баланс между надежностью, пропускной способностью и стоимостью системы.
В этой статье вы узнаете об основных идеях, лежащих в основе технологии RFID 13,56 МГц, в том числе о том, как карты и метки взаимодействуют со считывающими устройствами и что заставляет эту частоту работать именно так, как она работает.
Что такое радиометка 13,56 МГц?

RFID 13,56 МГц - это вид радиочастотной идентификации, работающий на частоте 13,56 мегагерц и относящийся к высокочастотному (HF) диапазону RFID. Она предназначена для связи на коротких расстояниях между считывающим устройством и небольшой электронной меткой с помощью электромагнитного поля, создаваемого вблизи антенны считывающего устройства.
Что представляет собой этот частотный диапазон
На частоте 13,56 МГц технология RFID работает в так называемом ближнем поле. Вместо того чтобы посылать сигналы далеко в пространство, как Wi-Fi или UHF RFID, считыватель создает магнитное поле вокруг своей антенны. Когда метка попадает в это поле, антенна внутри метки соединяется с ним и позволяет чипу обмениваться данными со считывателем. Такое поведение в ближнем поле является причиной того, что технология RFID 13,56 МГц в основном используется для близкого, намеренного взаимодействия, а не для обнаружения на большом расстоянии.
Почему он широко используется
Частота 13,56 МГц стала одной из самых распространенных частот RFID, поскольку она обеспечивает стабильный баланс между производительностью и стоимостью. Технология является зрелой, с устоявшимися стандартами и широким спектром доступных чипов и считывателей. Она поддерживает более сложный обмен данными, чем низкочастотная RFID, включая более высокую скорость передачи данных и встроенные функции безопасности во многих чипах. Это делает ее подходящей для систем, которым требуется нечто большее, чем простой серийный номер.
RFID против NFC
NFC основана на технологии RFID 13,56 МГц. Обе технологии используют одну и ту же частоту и схожие физические принципы. Разница заключается в том, что NFC добавляет особые правила связи и модели взаимодействия с пользователем, особенно для смартфонов и потребительских устройств. На практике многие метки 13,56 МГц предназначены для работы с NFC-считыватели, Но некоторые промышленные или специализированные высокочастотные RFID-метки соответствуют другим стандартам и могут не считываться телефонами.
Что такое карта или метка RFID 13,56 МГц?

Карта или метка RFID 13,56 МГц - это небольшое электронное устройство, состоящее из двух основных частей: чипа и антенны. В чипе хранится идентификационный номер и, во многих случаях, дополнительные данные. Антенна позволяет чипу связываться со считывающим устройством с помощью радиоволн на частоте 13,56 МГц.
Слово "метка" - это общий термин для обозначения любого транспондера RFID, работающего на этой частоте. Карта - это просто одна из форм метки, по форме напоминающая кредитную карту для удобства обращения с ней людей. Другие формы включают в себя наклейки, монеты и наручные браслеты. Все они работают по одному и тому же принципу и используют одну и ту же радиочастоту.
Эти метки обычно пассивны, то есть не имеют батареи. Когда считывающее устройство создает радиополе, метка использует эту энергию для питания своего чипа и отправки данных обратно. Сами по себе метки не могут передавать или хранить большие объемы информации. Их роль заключается в обеспечении беспроводной идентификации на коротком расстоянии и, в некоторых случаях, в хранении небольших блоков данных, которые система может считывать или обновлять.
В комплексной системе метка или карта выступает в качестве носителя данных, а считыватель и программное обеспечение занимаются обработкой и принятием решений. Такое разделение позволяет использовать один и тот же тип метки во многих различных системах, если считыватель и протокол совместимы.
Принцип работы меток RFID 13,56 МГц
RFID-метки 13,56 МГц работают за счет индуктивной связи между считывателем и меткой. Считыватель посылает высокочастотное переменное магнитное поле через свою антенну. Когда метка попадает в это поле, антенна внутри метки взаимодействует с ним и забирает небольшое количество энергии.
Чтобы отправить данные, метка не генерирует собственный радиосигнал. Вместо этого она изменяет то, как она нагружает магнитное поле, создаваемое считывателем. Это изменение может быть обнаружено считывателем и интерпретировано как цифровая информация. Таким образом, метка обменивается данными, модулируя поле считывателя, а не передавая сигнал самостоятельно.
Стандарты, используемые на частоте 13,56 МГц
Технология RFID 13,56 МГц не использует один-единственный метод связи. Она опирается на международные стандарты, которые определяют, как метки и считыватели общаются друг с другом. Эти стандарты определяют формат сигнала, скорость передачи данных и способ обмена командами. Если считыватель и метка не соответствуют одному стандарту, они не смогут общаться, даже если используют одну и ту же частоту.
ИСО 14443
ИСО 14443 является наиболее распространенным стандартом для радиометок ближнего радиуса действия на частоте 13,56 МГц. Он предназначен для коротких, намеренных взаимодействий, таких как прикосновение карты или телефона к считывателю. Этот стандарт используется во многих картах доступа, транспортных картах и системах на базе NFC. Он поддерживает быструю связь и может работать с чипами, обеспечивающими такие функции безопасности, как аутентификация и шифрование.
Стандарт ISO 14443 подразделяется на тип A и тип B, которые являются двумя техническими вариантами одного и того же стандарта. Для считывания конкретной метки считывающее устройство должно поддерживать нужный тип. Многие современные считыватели поддерживают оба типа, но это все равно необходимо проверить при проектировании системы.
ИСО 15693
ISO 15693 - еще один стандарт, используемый на частоте 13,56 МГц, но он рассчитан на более дальние расстояния считывания по сравнению с ISO 14443. Его часто называют “ближним” RFID, поскольку он работает в более широкой зоне вокруг антенны считывателя. Этот стандарт обычно используется в таких приложениях, как библиотечные системы и системы отслеживания активов, где метки считываются с небольшого расстояния без точного позиционирования.
Метки ISO 15693 обычно передают данные медленнее, чем метки ISO 14443, и, как правило, ориентированы на идентификацию и простое хранение данных, а не на расширенную безопасность.
Почему стандарты имеют значение
Стандарт определяет:
- Какие считыватели могут считывать метку
- Скорость обмена данными
- Имеются ли средства защиты
- Насколько стабильной будет связь
Использовать ту же частоту недостаточно. Считыватель 13,56 МГц должен поддерживать тот же стандарт, что и метка. По этой причине выбор правильного стандарта является одним из первых технических решений при создании системы RFID 13,56 МГц.
Типы меток и карт RFID 13,56 МГц
Метки и карты RFID 13,56 МГц можно классифицировать по двум основным признакам. Первая основана на технологии чипа внутри метки, которая определяет объем памяти, уровень безопасности и поддерживаемые стандарты. Другая основана на физической форме, которая определяет, как используется метка и насколько хорошо она сохраняется в различных условиях.
Типы по технологии производства микросхем
Карты MIFARE® RFID

Карты MIFARE основаны на стандарте ISO 14443 Type A и являются одним из наиболее широко распространенных семейств чипов HF RFID. Они предназначены для быстрой связи на очень малом расстоянии и поддерживают структурированный доступ к памяти. В зависимости от конкретного варианта MIFARE, карты могут обеспечивать базовое хранение данных в памяти или повышенную безопасность с аутентификацией и зашифрованным обменом данными.
Эти чипы предназначены для обработки частых транзакций и контролируемого взаимодействия с пользователями, поэтому они часто используются в крупных системах.
Сценарии применения: Системы общественного транспорта, карты контроля доступа, парковочные системы, удостоверения личности сотрудников и студентов.
Особенности: Поддержка ISO 14443 Тип A, Определяемые блоки памяти, опциональная криптографическая аутентификация, быстрое время отклика, широкая совместимость со считывающими устройствами.
RFID-карты NXP NTAG®
Чипы NTAG разработаны в соответствии со спецификациями NFC Forum Type 2 и оптимизированы для взаимодействия со смартфонами с поддержкой NFC. Они используют ISO 14443 Type A на физическом уровне, но организуют память таким образом, чтобы поддерживать стандартизированные форматы данных NFC.
В отличие от чипов, ориентированных на контроль доступа, чипы NTAG ориентированы на простой обмен данными с потребительскими устройствами, а не на многоуровневый контроль доступа.
Сценарии применения: Смарт-плакаты, информационные карточки товаров, маркетинговые метки, сопряжение устройств, интерактивные потребительские карточки.
Особенности: Совместимость со смартфонами NFC, простая структура памяти, поддержка записей данных NFC, низкие требования к энергопотреблению, предсказуемое поведение при чтении с близкого расстояния.
Карты защищенных микроконтроллеров (чипы класса DESFire)
Эти карты используют стандарт ISO 14443 Type A, но содержат внутренний микроконтроллер со специальным криптографическим оборудованием. Они поддерживают взаимную аутентификацию перед доступом к памяти и позволяют хранить на одной карте несколько независимых приложений, каждое из которых имеет собственные ключи и правила доступа.
Обмен данными может быть зашифрован на уровне протокола, а права доступа обеспечиваются самим чипом, а не программным обеспечением считывателя.
Сценарии применения: Транспортные карты с хранимой ценностью, государственные или корпоративные идентификационные карты, мультисервисные кампусные карты, платежные системы.
Особенности: Аппаратное шифрование, аутентификация по принципу "вызов-ответ", сегментированные области памяти, поддержка нескольких приложений на одной карте.
Карты RFID Vicinity по стандарту ISO 15693
Эти карты работают на той же частоте 13,56 МГц, но соответствуют стандарту ISO 15693, а не ISO 14443. Они рассчитаны на несколько большее расстояние считывания и более плотное расположение карты и считывателя. Скорость связи ниже, а модель памяти проще, чем у карт с близким расположением. Они обычно используются там, где требуется идентификация без точной привязки.
Сценарии применения: Библиотечные карточки, Карточки для отслеживания документов, карты доступа в условиях низкой безопасности, карты, связанные с активами.
Особенности: Большая дальность считывания ВЧ, более простая структура команд, стабильная работа при менее точном выравнивании, умеренный объем памяти.
Карты RFID с двумя интерфейсами
Карты с двумя интерфейсами сочетают бесконтактный интерфейс 13,56 МГц и физический контактный интерфейс на одном чипе. Оба интерфейса имеют доступ к одной и той же внутренней памяти и логике безопасности.
Это позволяет использовать одну и ту же карту как в контактных, так и в бесконтактных системах без дублирования учетных данных.
Сценарии применения: Государственные идентификационные карты, банковские карты, корпоративные идентификационные карты, которые должны работать как с контактными, так и с бесконтактными считывателями.
Особенности: Общая память между интерфейсами, единая модель безопасности, поддержка радиочастотной и электрической связи, согласованная идентификация в системах.
Типы по физической форме
Карты
RFID-карты Это плоские, жесткие метки, изготовленные из ПВХ или аналогичных материалов. Внутри карты в тонкий слой вмонтированы чип и антенна. Карточки удобно носить в кошельках или держателях для бейджей, и они обычно используются в тех случаях, когда метка должна находиться непосредственно в руках пользователя. Их антенна большего размера обычно обеспечивает стабильное и предсказуемое считывание на близком расстоянии.
Наклейки и этикетки

Наклейки и ярлыки тонкие и гибкие. Их можно прикреплять к таким предметам, как книги, упаковки или оборудование. Поскольку антенна имеет небольшой размер и напечатана на тонкой подложке, расстояние считывания обычно меньше, чем у карты. Эти метки выбирают, когда важен малый вес, малая толщина или скрытое размещение.
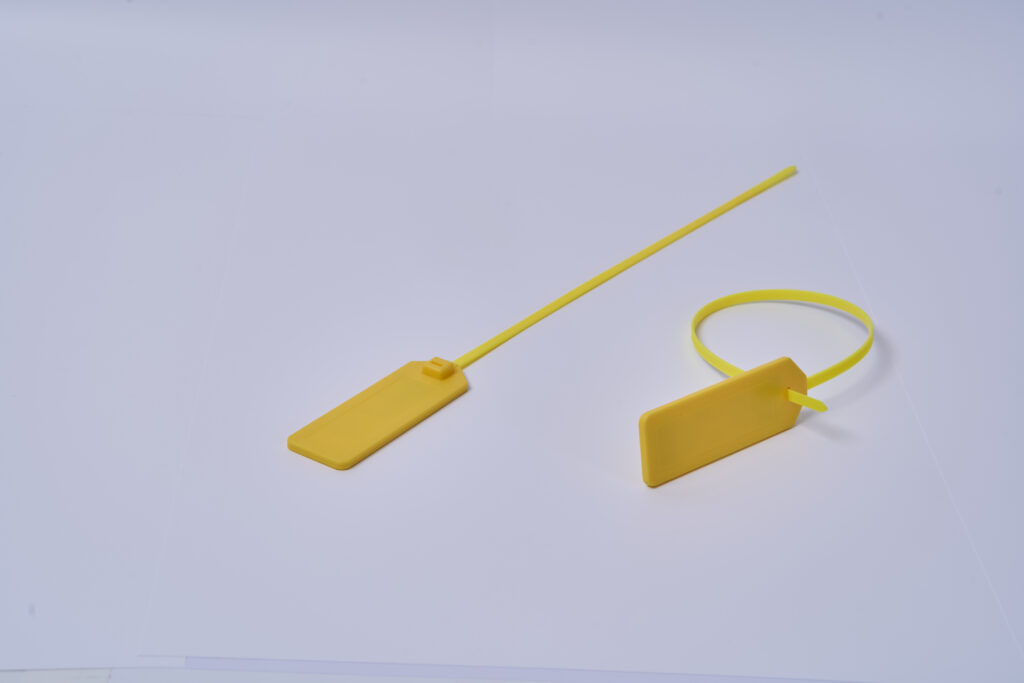
Бирки для монет и жесткие бирки
Монетные бирки и жесткие бирки заключены в пластиковые или смоляные корпуса. Они толще и прочнее, чем этикетки, и предназначены для более жестких условий эксплуатации. Такие метки часто используются, когда требуется устойчивость к ударам, влаге или обработке. Их прочная структура помогает защитить чип и антенну от повреждений.
Наручные браслеты и носимые метки

Наручные браслеты и носимые метки предназначены для ношения на теле. Чип и антенна встроены в силиконовые, тканевые или пластиковые ленты. Такие формы используются, когда метка должна оставаться с человеком в течение длительного времени. Форма их антенны адаптирована к изогнутым поверхностям, но близость к телу может повлиять на эффективность считывания, поэтому размещение и ориентация имеют значение.
Хотя эти формы выглядят по-разному, все они основаны на одном и том же базовом принципе связи на частоте 13,56 МГц. Основное различие заключается в форме и защите антенны, что определяет удобство использования метки и ее эффективность в конкретной ситуации.
Память и структура данных радиометок 13,56 МГц
Каждая RFID-метка или карта, работающая на частоте 13,56 МГц, содержит небольшой объем памяти внутри своего чипа. Эта память используется для хранения идентификационной информации и, во многих случаях, дополнительных пользовательских данных. От того, как организована эта память, зависит, что может хранить метка и как она может быть использована системой.
UID и память пользователя
Все метки имеют UID - уникальный идентификационный номер, установленный производителем чипа. Этот номер используется для отличия одной метки от другой. Помимо UID, многие метки содержат пользовательскую память, которая может записываться и обновляться системой. UID обычно фиксирован, а пользовательская память предназначена для данных приложения, таких как номер актива или код доступа.
Типичные размеры памяти
Объем памяти зависит от типа чипа. Некоторые метки хранят лишь небольшой объем данных, в то время как другие предлагают более обширные области памяти. Обычно размер памяти варьируется от нескольких десятков байт до нескольких килобайт. Даже самые большие чипы все равно предназначены для хранения коротких записей, а не больших файлов.
Как хранятся данные
Данные внутри метки не хранятся как единое целое. Они разделены на небольшие блоки, которые должны быть прочитаны или записаны вместе. Эти единицы расположены в определенном порядке, чтобы считывающее устройство знало, где искать конкретную информацию.
Блочная или страничная структура
В зависимости от конструкции микросхемы память организована в блоки или страницы. Каждый блок или страница вмещает фиксированное количество байт. Когда система записывает данные в метку, она записывает целые блоки или страницы за один раз. Такая структура помогает контролировать доступ и позволяет защищать определенные участки памяти, оставляя другие открытыми.
Что реально можно хранить
Поскольку память ограничена, теги не используются для хранения длинных текстов или изображений. В реальных системах они обычно хранят короткие фрагменты информации, такие как:
- идентификационный номер
- код продукта или актива
- небольшое значение статуса
- ссылка на запись в базе данных
Память метки лучше всего работает как компактный носитель данных, который поддерживает большую информационную систему, а не заменяет ее.
Особенности безопасности меток RFID 13,56 МГц
Безопасность в системах RFID 13,56 МГц реализована в самом чипе метки. Чип контролирует, кто может читать данные, кто может их записывать, и требуется ли аутентификация перед получением доступа. Разные чипы поддерживают разные модели безопасности, поэтому две метки с одинаковой частотой могут вести себя совершенно по-разному.
Открытая память и незащищенные теги
Некоторые метки, работающие на частоте 13,56 МГц, открывают свою память без какой-либо защиты. Любой совместимый считыватель может прочитать UID и память пользователя, а в некоторых случаях и записать новые данные. Такие метки полностью полагаются на внутреннюю систему, которая решает, можно ли доверять полученному идентификатору.
Такой подход используется, когда метка несет только контрольный номер, а реальная логика управления хранится в базе данных. Сама метка не проверяет считыватель и не ограничивает доступ.
Контроль доступа на основе пароля
Другие метки делят свою память на области, которые можно защитить паролем или ключом доступа.
Прежде чем считыватель сможет записать или прочитать защищенный блок, он должен отправить метке правильный пароль. Если пароль совпадает, метка временно разблокирует эту область памяти для доступа.
Этот метод предотвращает случайное или несанкционированное изменение данных, но не обеспечивает надежной защиты от опытных злоумышленников, поскольку пароль статичен и иногда может быть перехвачен или угадан, если система плохо спроектирована.
Криптографическая аутентификация
В более защищенных метках 13,56 МГц реализована криптографическая аутентификация. В этом случае метка и считыватель выполняют обмен "вызов-ответ" с использованием секретного ключа, хранящегося в чипе. Считыватель посылает метке случайный вызов. Метка шифрует этот вызов с помощью своего внутреннего ключа и возвращает результат. Считыватель проверяет ответ, используя тот же ключ. Только если результат правильный, метка разрешает доступ к защищенной памяти или командам.
Поскольку задача меняется каждый раз, переданные данные нельзя просто воспроизвести или скопировать. Это значительно усложняет клонирование на основе перехваченного трафика.
Правила доступа к памяти
Защищенные метки обычно определяют различные права доступа для разных областей памяти. Например:
- одна часть памяти может быть доступна для чтения любому человеку
- другая часть может потребовать аутентификации
- запись может быть ограничена только для аутентифицированных читателей
- некоторые блоки могут быть постоянно заблокированы после программирования
Эти правила выполняются чипом, а не программным обеспечением считывателя. Даже если кто-то создаст свой собственный считыватель, чип откажет в доступе, если не будут соблюдены необходимые условия.
Поведение против клонирования
Базовое клонирование копирует видимые данные с одной метки на другую. Защищенные чипы 13,56 МГц разработаны таким образом, что аутентификация зависит не только от хранимой памяти, но и от внутреннего секретного материала, который не может быть считан.
Даже если две метки содержат одну и ту же пользовательскую память, они не будут вести себя одинаково во время зашифрованной аутентификации. Это позволяет системе определить, используется ли настоящая или скопированная метка.
Почему уровень безопасности имеет значение
В простых системах, таких как базовая идентификация или отслеживание, безопасность может не иметь решающего значения, поскольку метка содержит только номер, а система проверяет этот номер в другом месте.
В системах контроля доступа, продажи билетов или оплаты сама метка становится частью границы доверия. Если метку можно скопировать, систему можно обойти. Для таких случаев требуются чипы с криптографической аутентификацией и контролируемым доступом к памяти, так что одного владения меткой без корректного внутреннего поведения недостаточно.
На практике выбор RFID-метки 13,56 МГц означает выбор модели безопасности, а не только частоты. Чип определяет, будут ли данные открыто читаться, защищаться паролями или охраняться криптографической аутентификацией, и этот выбор напрямую влияет на устойчивость системы к копированию и неправомерному использованию.
Преимущества карт RFID 13,56 МГц

По сравнению со старыми технологиями, такими как карты с магнитной полосой и штрих-кодом, карты RFID 13,56 МГц ускоряют идентификацию и упрощают доступ, поскольку работают без физического контакта и поддерживают более надежную защиту данных. В системах с большим количеством ежедневных пользователей эти различия быстро проявляются в скорости, надежности и долгосрочном обслуживании.
Быстрые транзакции с меньшими трудностями
Карту с магнитной полосой необходимо провести в правильном направлении и с нужной скоростью. Карта со штрих-кодом должна быть выровнена так, чтобы сканер мог четко ее видеть. Карту с радиометкой 13,56 МГц нужно только поднести к считывателю. Такое простое взаимодействие сокращает время сканирования, снижает вероятность ошибок пользователей и позволяет не задерживать очереди в таких оживленных местах, как офисы, кампусы, спортивные залы и транзитные пункты.
Меньше износа и меньше проблем с заменой
Магнитные полосы изнашиваются от многократного проведения по ним пальцем и могут выйти из строя после царапин, загрязнения или изгиба. Карты со штрих-кодом могут стать нечитаемыми, если напечатанный код поцарапан, выцвел или закрыт. Карты RFID 13,56 МГц не используют для считывания поверхностную полосу или печатный код, поэтому обычное ежедневное обращение с ними приводит к меньшему количеству сбоев при считывании. Это увеличивает срок службы карт в условиях интенсивного использования и снижает объем работ по замене и поддержке.
Лучшие возможности защиты по сравнению с картами с полосой или штрих-кодом
Карты с магнитной полосой и штрих-кодом обычно несут данные в форме, которую легко скопировать. Многие чипы RFID-карт 13,56 МГц поддерживают функции безопасности, которые гораздо сложнее скопировать, например аутентифицированный доступ к данным и зашифрованную связь. Это важно в тех случаях, когда скопированная карта представляет собой реальный риск, например, при входе в здание, выдаче пропусков персоналу, системах членства и контролируемых услугах.
Не требуется прямая видимость
Сканирование штрих-кода требует четкого представления напечатанного кода. Это делает его чувствительным к ориентации, освещению, повреждениям поверхности и способу подачи карты. RFID не требует прямой видимости. Карту часто можно считать через бумажник или держатель бейджа, и она не зависит от того, что камера или лазер имеют четкий обзор напечатанного рисунка. Это делает реальное использование более плавным и последовательным.
Одна карта может поддерживать больше функций
Карты с магнитной полосой и штрих-кодом обычно ограничиваются идентификатором или простым номером для поиска. Многие карты RFID 13,56 МГц могут хранить дополнительные данные и поддерживать более сложные рабочие процессы, в зависимости от типа чипа. Именно поэтому одна и та же технология карт может использоваться для контроля доступа, посещаемости, подтверждения членства и других контролируемых операций в одной и той же организации без изменения базового формата карты.
Легче интегрировать в современные экосистемы
Технология RFID 13,56 МГц широко используется и имеет развитую цепочку поставок карт и считывателей. Во многих случаях она также может быть согласована с рабочими процессами на основе NFC, что упрощает подключение карточных систем к современным устройствам и программным платформам, когда это необходимо. Это практическое преимущество для организаций, которым нужна долгосрочная поддержка и гибкость, а не закрытый, устаревший формат карт.
Области применения карт RFID 13,56 МГц
Карты RFID 13,56 МГц в основном используются в ситуациях, когда людям необходимо быстро и многократно идентифицировать себя или подтвердить разрешение. Малая дальность считывания и бесконтактный режим работы делают их пригодными для контролируемого взаимодействия между людьми и системами.
Карты доступа в здания и офисы
Многие офисы, заводы и жилые дома используют RFID-карты в качестве дверных ключей. Сотрудники или жильцы предъявляют карту считывающему устройству, чтобы отпереть двери, въехать на парковку или пройти через ворота безопасности. Карта удостоверяет личность человека, а правами доступа управляет система.
Карты общественного транспорта
Карты метро, автобусные карты и проездные билеты обычно используют технологию RFID 13,56 МГц. Пассажиры касаются карты на выходе или на бортовых считывающих устройствах, чтобы войти и выйти. Карта может хранить основные данные о поездках или просто служить идентификатором, связанным с внутренней системой, которая отслеживает поездки и баланс.
Студенческие и кампусные удостоверения личности
Школы и университеты выпускают RFID-карты в качестве студенческих удостоверений. Эти карты используются для входа в здания, получения книг в библиотеке, регистрации посещаемости или доступа к услугам кампуса. Одна карта часто заменяет несколько бумажных или пластиковых удостоверений личности.
Карточки-ключи от гостиничных номеров
Карты-ключи для гостиниц используют технологию RFID 13,56 МГц для разблокировки гостевых номеров и иногда лифтов. Каждая карта программируется на определенный период проживания и номер комнаты. По окончании проживания карта может быть перепрограммирована для следующего гостя.
Карты членства и лояльности
Тренажерные залы, клубы и частные заведения используют RFID-карты для идентификации членов на входе. Карта подтверждает статус участника и может быть связана с записями о посещениях или использовании услуг без ручной регистрации.
Карточки учета рабочего времени и посещаемости
На заводах, в офисах и на складах карты RFID используются в системах учета рабочего времени. Работники подносят карту к считывающему устройству для автоматической записи времени начала и окончания работы, что сокращает ручной документооборот.
Бейджи для мероприятий и посетителей
На конференциях, выставках и контролируемых мероприятиях посетителям выдаются RFID-карты или бейджи. Эти карты разрешают вход в определенные зоны и могут помочь организаторам проверять посещаемость или контролировать доступ без визуального осмотра.
Бесконтактные платежные карты
Многие современные банковские карты используют технологию RFID на частоте 13,56 МГц для поддержки операций tap-to-pay. Вместо того чтобы вставлять карту в терминал или проводить пальцем по магнитной полосе, пользователь держит карту рядом со считывающим устройством. Карта и терминал обмениваются необходимыми данными о транзакциях по беспроводной связи в пределах короткого расстояния. Этот метод сокращает время транзакции и позволяет избежать механического контакта, что ускоряет процесс оформления заказа в магазинах и транзитных системах, где ежедневно обрабатывается большое количество платежей.
Расстояние считывания и факторы эффективности RFID-меток 13,56 МГц
Расстояние считывания RFID-метки 13,56 МГц естественно мало, поскольку эта частота работает за счет связи магнитного поля, а не дальних радиоволн. В большинстве реальных систем для работы метку необходимо поднести близко к считывателю.
Типичное расстояние для чтения на практике
Для распространенных систем карт и бейджей, основанных на стандарте ISO 14443, полезное расстояние считывания обычно составляет от 3 до 7 сантиметров. При хорошем выравнивании и удачно спроектированной антенне считывателя оно может достигать 10 сантиметров.
Для меток ISO 15693, рассчитанных на несколько больший радиус действия, типичные расстояния составляют от 10 до 30 сантиметров, а в хорошо оптимизированных системах с большими антеннами они могут достигать примерно 1 метра. Такая большая дальность не характерна для карт типа tap и используется в основном в библиотеках и системах отслеживания активов.
Размер и форма антенны внутри метки
Антенна - это часть метки, которая улавливает энергию поля считывателя. Большая площадь антенны, как правило, сильнее взаимодействует с магнитным полем, что помогает чипу получать достаточно энергии для работы. Плоские карты обычно содержат петлевую антенну, которая проходит по краю карты, что обеспечивает более стабильную работу, чем очень маленькие этикетки или монетные метки. Компактные метки работают, но у них, как правило, более короткое и менее стабильное расстояние считывания.
Ориентация метки относительно поля считывателя
Технология RFID 13,56 МГц основана на связи магнитных полей, а не на дальних радиоволнах. Для эффективной связи антенна метки должна быть выровнена с линиями магнитного поля считывателя. Если повернуть или наклонить метку так, чтобы плоскость ее антенны была плохо выровнена, индуцированная энергия падает, и метка может не активироваться. Вот почему одна и та же карта может легко считываться в одном положении и не срабатывать при повороте набок.
Металл рядом с биркой
Металл сильно искажает магнитные поля. Когда метка 13,56 МГц размещается непосредственно на металле или очень близко к нему, диаграмма поля антенны изменяется, и передача энергии становится неэффективной. Это часто значительно сокращает расстояние считывания или вовсе препятствует считыванию. При установке меток на металлические поверхности требуются специальные конструкции меток или распорки.
Вода и человеческое тело
Вода поглощает электромагнитную энергию в этом диапазоне частот. Поскольку человеческое тело содержит большой процент воды, метки, носимые в карманах, на запястье или прижатые к коже, могут демонстрировать пониженную эффективность. Наручные браслеты и носимые метки имеют форму антенны, компенсирующую этот эффект, но близость к телу все равно ограничивает их полезное расстояние по сравнению с картой free-air.
Минимальная энергия активации чипа
Пассивная метка может работать только тогда, когда она получает от поля считывателя энергию, достаточную для питания ее чипа. Если напряженность поля в месте расположения метки ниже этого порога, метка вообще не может реагировать. Для надежной работы чипов с более высокими требованиями к мощности требуется более сильная связь или более близкое расстояние. Это устанавливает жесткое ограничение на то, как далеко может быть считана метка данной конструкции.
Окружающая среда
Расположенное рядом электронное оборудование, проводка или крупные проводящие предметы могут нарушить магнитное поле вокруг считывателя. Температура и влажность обычно не мешают работе метки, но со временем они могут несколько изменить поведение антенны или свойства материала. В контролируемых системах внутри помещений производительность стабильна; в промышленных условиях или в местах скопления людей отклонения более распространены.
Намеренное сокращение дистанции
Малое рабочее расстояние радиометок 13,56 МГц - это не недостаток, а конструктивная особенность. Она позволяет пользователям контролировать момент считывания метки, поднося ее близко к считывателю, и снижает риск непреднамеренного сканирования. Этот контролируемый диапазон является одной из причин широкого использования технологии в системах персональной идентификации и доступа.
Как выбрать правильную карту RFID 13,56 МГц

При выборе RFID-карты 13,56 МГц следует исходить из того, как она будет использоваться в системе. Карты с одинаковой частотой могут отличаться по уровню безопасности, памяти и поведению при взаимодействии, поэтому эти факторы необходимо оценить перед покупкой.
Сценарий применения
От того, что представляет собой карта и как система использует ее, напрямую зависит, какими техническими возможностями должна обладать карта.
Если карта используется для контроля доступа или разрешения, например, для входа в дверь, парковочных ворот или идентификации персонала, она является частью процесса контроля. Она должна надежно срабатывать на очень коротких расстояниях и обычно должна поддерживать аутентификацию на уровне чипа. В системах такого типа считывающее устройство часто принимает немедленное решение на основе реакции карты, поэтому поведение карты должно быть последовательным и предсказуемым.
Требования к карте:
- Должна поддерживаться аутентификация на карте (а не просто считываемый идентификатор)
- Должен стабильно вести себя на очень коротких расстояниях для использования крана
- Обычно требуется контролируемый доступ к памяти и возможность защиты от клонирования
Подходящий класс карты:
- Карты с криптографической аутентификацией (вызов-ответ с использованием секретных ключей)
- Предназначен для работы с кранами по стандарту ISO 14443
Если карта используется только для идентификации, например для учета посещаемости, проверки членства или регистрации посетителей, она в основном предоставляет идентификатор внутренней системе. Логика системы обрабатывается программным обеспечением, а не самой картой. Сложные функции на карте обычно не нужны, главное требование - стабильное считывание и уникальный идентификатор.
Требования к карте:
- Стабильный уникальный идентификатор
- Надежное считывание показаний крана
- Нет необходимости в логике принятия решений на карте
Подходящий класс карты:
- Карты на основе UID
- Простые карты памяти, используемые только в качестве носителей идентификационных данных
Если карта используется для краткосрочного или одноразового применения, например, для бейджей на мероприятиях или временных пропусков, срок службы и возможность повторного использования ограничены. Плавное взаимодействие с краном и низкая стоимость устройства обычно важнее, чем долговечность или расширенные возможности.
Требования к карте:
- Плавное взаимодействие при нажатии
- Низкая стоимость единицы продукции
- Нет необходимости в длительном сроке службы или сложных внутренних функциях
Подходящий класс карты:
- Основные карты, совместимые с NFC
- Простые карты крана ISO 14443 без расширенных функций безопасности
Уровень безопасности
Безопасность на частоте 13,56 МГц определяется поведением чипа, а не частотой. Карты, использующие одну и ту же частоту, могут полностью различаться по способам аутентификации, защиты памяти и защиты от клонирования. Поэтому выбор системы безопасности зависит от того, должна ли сама карта подтверждать свою подлинность или системе нужен только идентификатор, который проверяется программным обеспечением.
Если карта используется для непосредственного предоставления доступа или ценности, например, в дверных системах, парковочных барьерах, транзитных воротах или автономных пунктах проверки, карта сама должна подтвердить свою подлинность. В таких системах считывающее устройство не может полагаться на сервер для проверки карты в режиме реального времени и должно принимать решение немедленно, основываясь на поведении карты во время обмена данными. Это означает, что карта должна демонстрировать подлинное внутреннее поведение, а не просто представлять читаемый номер.
Требования к карте:
- Должен выполнять криптографическую аутентификацию с помощью вызова-ответа
- Должны хранить секретные ключи внутри, которые невозможно извлечь
- Должна поддерживать защищенные команды или зашифрованную связь
- Доступ к памяти должен быть ограничен ключами, а не открыто доступен для чтения
Подходящий класс карты:
- Карты, использующие аутентификацию на основе AES
- Карты с раздельными приложениями или файлами и независимыми ключами
- Карты, предназначенные для безопасного управления по стандарту ISO 14443
Если карта используется в контролируемой системе, где каждая транзакция проверяется внутренним сервером, например в системах учета рабочего времени сотрудников, библиотечных системах или при проверке членства в профсоюзе, карта в основном служит источником данных. Логика системы работает в программном обеспечении, и карте не нужно самостоятельно подтверждать подлинность. Сервер решает, являются ли полученные данные карты приемлемыми.
Требования к карте:
- Должен обеспечивать стабильный и уникальный идентификатор
- Может использоваться базовая защита памяти для обеспечения целостности данных
- Не требует криптографической аутентификации "вызов-ответ".
Подходящий класс карты:
- Карты с памятью, защищенной паролем или ключом
- Карты, используемые в основном как носители идентификационных данных с ограниченной внутренней логикой
Если карта используется только в качестве эталонного маркера в ситуациях с низким уровнем риска, таких как внутренняя маркировка, временные учетные данные или простое отслеживание, когда дублирование не приводит к прямым потерям, система не зависит от карты для подтверждения подлинности. Карта должна лишь надежно реагировать на запросы и предоставлять идентификатор.
Требования к карте:
- Должен предоставить читаемый UID
- Должен стабильно реагировать на короткие дистанции
- Не нуждается в защищенных командах и функциях аутентификации
Подходящий класс карты:
- Карты только с UID
- Простые карты памяти без безопасной аутентификации
Требование к хранению
Количество данных на карте зависит от того, что система ожидает от карты. Некоторые системы используют карту только в качестве идентификатора и хранят всю информацию в базе данных. Другим системам требуется, чтобы на карте хранились структурированные записи, счетчики или несколько полей данных, которые обновляются с течением времени.
Если карта используется только для предоставления идентификатора, который ссылается на внутреннюю запись, например, для регистрации посещаемости, проверки членства или регистрации посетителей, система не полагается на то, что карта будет содержать значимые данные. В базе данных хранятся имена, балансы или разрешения, а карта служит лишь ссылкой.
Требования к карте:
- Нужен только стабильный UID
- Нет необходимости в структурированной памяти пользователя
- Нет необходимости в частых циклах записи
Подходящий класс карты:
- Карты на основе UID
- Простые карты памяти, используемые только в качестве идентификаторов
Если карта должна хранить на чипе небольшие записи, такие как правила доступа, счетчики билетов или короткие значения состояния, которые считываются и обновляются считывателем, память должна поддерживать организованное хранение и контролируемый доступ. Системная логика может по-прежнему существовать в программном обеспечении, но карта несет рабочие данные.
Требования к карте:
- Память пользователя, разделенная на блоки или файлы
- Поддержка повторяющихся операций чтения и записи
- Дополнительный контроль доступа к каждой области памяти
Подходящий класс карты:
- Карты с блочной или файловой структурой памяти
- Карты, поддерживающие управление доступом на уровне секторов или страниц
Если карта используется для хранения нескольких элементов данных, таких как история поездок, баллы за лояльность или специфические записи приложения, память должна быть достаточно большой и логически разделенной. В таких системах часто используются файлы приложений, а не необработанные блоки, что позволяет управлять различными областями данных независимо друг от друга.
Требования к карте:
- Больший объем памяти
- Разделение приложений или файлов
- Независимые права доступа к каждой области данных
Подходящий класс карты:
- Карты с моделями памяти на основе приложений
- Карты, поддерживающие многофайловые структуры с отдельными ключами
Если предполагается, что карта будет работать в автономном режиме и хранить информацию о значении или состоянии без постоянного доступа к серверу, целостность памяти становится критически важной. Карта должна не только хранить данные, но и защищать их от перезаписи или воспроизведения.
Требования к карте:
- Защищенные команды записи
- Управляемые правила обновления
- Поддержка безопасного хранения данных
Подходящий класс карты:
- Карты с защищенными операциями с памятью
- Карты, предназначенные для хранения транзакций или состояний
Совместимость с телефонами (должна ли карта работать со смартфонами)
То, что карта должна считываться телефоном, меняет технические ограничения на возможные типы чипов. Смартфоны не ведут себя как промышленные считывающие устройства. Если карта должна считываться смартфоном, например, для мобильной регистрации, цифровых билетов, смарт-постеров или взаимодействия с пользователем через приложение, чип должен соответствовать стандартам и наборам команд NFC, поддерживаемым телефоном.
Требования к карте:
- Должны следовать протоколам, совместимым с NFC
- Должен поддерживать передачу данных в стиле крана ISO 14443
- Ответ должен быть в пределах временных ограничений NFC телефона
- Команды должны соответствовать поддерживаемым телефоном наборам команд
Подходящий класс карты:
- Карты, совместимые с NFC
- Карты, предназначенные для чтения со смартфона
- Карты ISO 14443 типа A или типа B, поддерживаемые телефонами
Если карта используется только с фиксированными считывателями, такими как контроллеры дверей, часы времени или считыватели ворот, нет необходимости ограничивать выбор только совместимыми с телефоном чипами. В таких системах можно использовать более широкий спектр HF-чипов с пользовательскими командами или промышленным поведением считывателя.
Требования к карте:
- Совместимость с развернутой моделью считывателя
- Не требуется поддержка команд на смартфоне
- Могут использоваться запатентованные или расширенные инструкции
Подходящий класс карты:
- Высокочастотные карты, предназначенные для считывания
- Карты, предназначенные для промышленных или встраиваемых считывателей
Если карта используется в смешанной среде, где она должна работать как с телефонами, так и со специальными считывателями, чип нужно выбирать тщательно. Обе стороны должны поддерживать один и тот же протокол и метод защиты, иначе одна из сторон не сработает.
Требования к карте:
- Должен быть доступен для чтения как телефонными NFC, так и стационарными считывателями
- Должны использовать только стандартные наборы команд
- Метод безопасности должен поддерживаться обоими
Подходящий класс карты:
- NFC-совместимые карты со стандартной аутентификацией
- Карты, использующие широко поддерживаемое поведение ISO 14443
Стиль взаимодействия
От того, как пользователь подносит карту к считывающему устройству, зависит, какое коммуникационное поведение должна поддерживать карта.
Если карта используется в системах на основе кранов, таких как панели доступа, турникеты или считыватели платежного типа, пользователь намеренно подносит карту на короткое время очень близко к поверхности считывателя. Система ожидает быстрого отклика и контролируемого сцепления.
Требования к карте:
- Оптимизирован для очень короткого расстояния чтения
- Быстрое время отклика
- Стабильное поведение при совмещении с антенной считывателя
- Предназначен для точного, целенаправленного представления
Подходящий класс карты:
- Карты с краном по стандарту ISO 14443
- Карты, предназначенные для работы на близком расстоянии в стиле NFC
Если карта используется в системах со свободным расположением, таких как библиотечные книги, папки с документами или сложенные в стопку предметы, карта может быть неточно совмещена со считывающим устройством. Считывающее устройство сканирует область, а не одну точку.
Требования к карте:
- Устойчивость к ориентации и позиционированию
- Можно использовать на чуть больших расстояниях по ВЧ
- Меньше зависит от точного выравнивания антенны
Подходящий класс карты:
- Карты, предназначенные для работы в режиме близости
- Карты, предназначенные для взаимодействия в стиле ISO 15693
Если карта должна работать как в режиме крана, так и в свободном положении, например, общие карты, используемые людьми, а также считываемые киосками или устройствами инвентаризации, ее поведение должно быть предсказуемым в обоих случаях.
Требования к карте:
- Последовательная реакция на различные типы считывателей
- Отсутствие зависимости от высоконастроенной антенной связи
- Стандартное поведение команды
Подходящий класс карты:
- Карты с поддержкой широко распространенных ВЧ-стандартов
- Карты, разработанные для смешанных читательских сред
Среда использования
От того, где и как физически используется карта, зависит, будет ли стандартная антенна карты работать так, как ожидается. Одна и та же карта 13,56 МГц может вести себя совершенно по-разному, когда ее кладут на металл, носят на теле или подвергают воздействию влаги и перепадов температуры.
Если карта установлена на металлических поверхностях или очень близко к ним, таких как панели механизмов, шкафчики или рамы автомобилей, магнитное поле искажается, и передача энергии резко снижается. Обычная карта-вкладыш, которая работает на открытом воздухе, может стать нечитаемой после прикрепления к металлу.
Требования к карте:
- Конструкция антенны, устойчивая к металлическим помехам или поддерживаемая распорным материалом
- Стабильная связь, несмотря на наличие рядом проводящих поверхностей
- Постоянная производительность при закреплении на жестком объекте
Подходящий класс карты:
- Карты, предназначенные для использования в металлических корпусах
- Платы со специальным расположением антенн или изолирующими слоями
Если карта носится на теле или находится в тесном контакте с кожей, как, например, браслеты или держатели для бейджей, ткани человека поглощают часть радиочастотной энергии и уменьшают расстояние считывания. Антенна должна быть сформирована и настроена на близость к телу, а не на свободный воздух.
Требования к карте:
- Антенна, адаптированная к нагрузке на тело
- Надежный отклик на малом расстоянии, несмотря на поглощение
- Форм-фактор, сохраняющий стабильную форму антенны
Подходящий класс карты:
- Карты или носимые устройства, предназначенные для использования на теле
- Карты с геометрией антенны, оптимизированной для тесной связи
Если карта используется во влажной, сырой или грязной среде, например в плавательных бассейнах, уличных воротах или на промышленных объектах, физическая защита становится критически важной. Попадание влаги и загрязнение поверхности могут повредить инкрустацию и вызвать прерывистое считывание.
Требования к карте:
- Герметичная или ламинированная конструкция
- Устойчивость к проникновению воды и грязи
- Стабильная структура антенны при воздействии влаги
Подходящий класс карты:
- Полностью заламинированные или запечатанные карты
- Карты, предназначенные для использования вне помещений или в промышленных условиях
Если карта подвергается перепадам температуры или механическим нагрузкам, например, в холодильных камерах, при транспортировке на открытом воздухе или ежедневном сгибании в кошельках, инкрустация и чип должны оставаться неповрежденными и настроенными в течение долгого времени.
Требования к карте:
- Материалы для вкладок, устойчивые к тепловому расширению и сжатию
- Механическая стабильность при изгибе или вибрации
- Отсутствие зависимости от хрупких печатных антенных трасс
Подходящий класс карты:
- Карты с усиленными вставками
- Карты, рассчитанные на длительную эксплуатацию в условиях окружающей среды
Упаковка
Упаковка определяет, как физически защищены чип и антенна и как радиочастотное поле покидает карту. Две карты, использующие один и тот же чип, могут вести себя совершенно по-разному, если их заламинировать, встроить или заключить в разные материалы. Поэтому упаковка - это и механический, и радиочастотный выбор конструкции, а не просто выбор внешнего вида.
Если карта должна быть тонкой и гибкой, например, для бумажных карт или вкладышей для бейджей, антенна обычно изготавливается из вытравленных или напечатанных металлических слоев внутри структуры из ПВХ или ПЭТ. Это хорошо подходит для стандартного использования в кранах, но обеспечивает ограниченную защиту от изгибов и нагрева.
Требования к карте:
- Тонкая вставка со стабильной геометрией антенны
- Ламинирование, которое не смещает положение антенны
- Предсказуемая радиочастотная настройка для использования кранов малого радиуса действия
Подходящий тип упаковки:
- Стандартные ламинированные карты из ПВХ или ПЭТ
- Тонкие карточки-вкладыши для использования в бейджах или бумажниках
Если карта должна быть жесткой и ударопрочной, например, для промышленных бейджей или удостоверений многократного использования, вкладыш должен быть механически изолирован от нагрузок. Трещины или деформация антенной петли напрямую влияют на эффективность считывания.
Требования к карте:
- Жесткий корпус, предотвращающий деформацию антенны
- Вкладыш полностью встроен и защищен
- Стабильное соединение при физическом воздействии
Подходящий тип упаковки:
- Карты с твердым пластиковым корпусом
- Многослойные карты, изготовленные методом литья под давлением
Если карта должна быть водонепроницаемой или химически стойкой, например, для наружных систем, плавательных средств или промышленных процессов очистки, вставка должна быть герметичной, чтобы влага не могла попасть на контакты антенны или чипа.
Требования к карте:
- Полностью герметичная структура без открытых слоев
- Отсутствие следов влаги по краям карты
- Материалы, которые не впитывают воду
Подходящий тип упаковки:
- Полностью герметичные карты
- Герметичные корпуса карт из смолы или полимера
Если карта используется в качестве этикетки или встраивается в какой-либо объект, например, внутрь пластикового корпуса, билета или корпуса оборудования, упаковка влияет на то, как антенна соединяется со считывателем через этот материал.
Требования к карте:
- Антенна, настроенная на материал носителя
- Стабильная ориентация после встраивания
- Отсутствие проводящих слоев вблизи антенны
Подходящий тип упаковки:
- Карты только с вкладышами для встраивания
- Конструкции карт в стиле этикетки
Расходы
Стоимость - это не только цена единицы карты. Она зависит от типа чипа, объема памяти, функций безопасности и способа упаковки. Карты с одинаковой частотой могут сильно отличаться по цене, поскольку внутренняя микросхема и физическая конструкция определяют сложность и стоимость их производства.
Если карта используется в больших количествах с низким уровнем риска, например, в качестве временных бейджей, простых карточек посещаемости или внутренних этикеток, система не зависит от безопасности самой карты. В таких случаях главная цель - минимизировать затраты при сохранении стабильного поведения считывания.
Требования к карте:
- Базовый UID или простая память
- Отсутствие криптографической аутентификации
- Стандартная конструкция карты
Стоимостные характеристики:
- Самая низкая цена за единицу продукции
- Подходит для массового распространения
- Легко заменить в случае потери или повреждения
Если карта используется в системах среднего масштаба с умеренным риском, таких как бейджи сотрудников, библиотечные карточки или членские билеты, система может по-прежнему полагаться в основном на внутреннее программное обеспечение, но копирование карты не должно быть совсем уж тривиальным.
Требования к карте:
- Защищенная память или простая аутентификация
- Стабильное поведение крана
- Стандартная или слегка усиленная упаковка
Стоимостные характеристики:
- Средняя цена
- Сбалансированность между функциями и бюджетом
- Приемлемо для контролируемых групп пользователей
Если карта используется в системах с высокой ценностью или повышенным риском, таких как контроль доступа в закрытые зоны, платный транспорт или автономная проверка, она должна активно участвовать в принятии решений по обеспечению безопасности. Это всегда увеличивает стоимость, поскольку чип должен поддерживать криптографические операции и защищенные структуры памяти.
Требования к карте:
- Криптографическая аутентификация (вызов-ответ)
- Внутренние секретные ключи
- Управляемый доступ к памяти
Стоимостные характеристики:
- Самая высокая цена за единицу продукции
- В первую очередь, это обусловлено возможностями чипа, а не внешним видом
- Оправдано снижением риска и доверием к системе
Часто задаваемые вопросы
Для чего используется частота 13,56 МГц?
Частота 13,56 МГц используется для бесконтактной идентификации на коротком расстоянии и обмена небольшими данными. Это наиболее распространенная частота для высокочастотных RFID-систем, в которых пользователь намеренно подносит карту или метку к считывающему устройству. Типичные примеры использования в реальном мире включают карты доступа в здания, карточки-ключи от гостиниц, транзитные билеты, библиотечные метки, пропуска на мероприятия, а также взаимодействие с NFC, например, прикосновение телефона к терминалу или сканирование метки NFC. Причина, по которой эта полоса подходит для этих целей, заключается в том, что она работает в ближнем поле, используя магнитную связь, поэтому зона считывания естественно короткая и контролируемая, что полезно для взаимодействия в стиле tap.
Является ли 13,56 МГц RFID или NFC?
13,56 МГц - это частота. И RFID, и NFC могут работать на частоте 13,56 МГц. RFID - это более широкая категория радиочастотной идентификации. NFC - это особый набор стандартов и моделей поведения, созданный на основе высокочастотной радиометки 13,56 МГц для потребительских устройств, особенно смартфонов. Таким образом, 13,56 МГц может использоваться системами RFID без NFC, а также системами NFC.
13,56 МГц — это то же самое, что NFC?
Нет. NFC всегда использует 13,56 МГц, но системы 13,56 МГц не всегда являются NFC. На практике телефон поддерживает только определенные протоколы и команды 13,56 МГц. Вот почему некоторые карты и метки, работающие на частоте 13,56 МГц, могут считываться телефонами, а другие - нет, несмотря на то, что они работают на одной частоте.
На каком расстоянии можно считать RFID-карту, работающую на частоте 13,56 МГц?
Для большинства карт 13,56 МГц, используемых в системах ответвителей, типичное расстояние считывания составляет несколько сантиметров, обычно от 2 до 10 см. При использовании более крупных антенн считывателя, хорошо настроенных антенн карты и благоприятных условий некоторые системы могут достигать десятков сантиметров. Достижение расстояния около 1 метра не является типичным для стандартных карт стандарта ISO 14443 и обычно связано с различными типами высокочастотных меток, специальными конструкциями антенн или специализированными конфигурациями считывателей и антенн. Ключевым моментом является то, что 13,56 МГц рассчитан на связь в ближнем поле, поэтому дальность действия мала по своей конструкции и сильно зависит от размера антенны, выравнивания, близлежащего металла и присутствия человеческого тела.
Являются ли карты RFID 13,56 МГц взаимозаменяемыми с картами других частот?
Нет. Карту, работающую на частоте 13,56 МГц, нельзя считывать считывателем, работающим на частоте 125 кГц, и нельзя считывать считывателем, работающим на частоте UHF. Частота считывателя должна совпадать с частотой карты. Кроме того, даже если частота совпадает, карта и считыватель должны поддерживать один и тот же протокол. Совпадение частот необходимо, но не всегда достаточно.
Можно ли копировать карты RFID 13,56 МГц?
Это зависит от типа чипа и от того, как система использует карту.
Если карта содержит только идентификатор UID или использует простую память со слабой защитой, скопировать видимые данные не составит труда. В таких случаях клонирование часто означает дублирование идентификатора или блоков данных на другой совместимый чип.
Если карта использует криптографическую аутентификацию, скопировать ее гораздо сложнее, поскольку она содержит секретные ключи, которые невозможно считать. Такие карты подтверждают подлинность, выполняя процесс ответа на вызов, поэтому совпадения с видимой памятью недостаточно. В системах, которые полагаются на такое криптографическое поведение, клонированная карта, которая только копирует данные, не пройдет проверку подлинности.
Поэтому точное правило таково: 13,56 МГц не определяет устойчивость к копированию. Это делает модель защиты чипа.
В чем разница между 13,56 МГц и 125 кГц?
Основное различие заключается в том, как они сочетаются друг с другом и что это означает для производительности и типичного использования.
13,56 МГц - это высокая частота RFID. Как правило, она поддерживает более высокую скорость передачи данных, более стандартизированные протоколы в стиле смарт-карт, а также более широкий спектр чипов с большим объемом памяти и более надежными средствами защиты. Она широко используется в картах с краном, билетах и вариантах использования, связанных с NFC.
125 кГц - это низкая частота RFID. Как правило, она предлагает более простую функциональность, часто просто идентификационный номер, с более низкой скоростью передачи данных и меньшим количеством расширенных возможностей безопасности во многих распространенных реализациях. Она часто используется для базового контроля доступа и простой идентификации, где стоимость и надежность имеют большее значение, чем объем данных или расширенная криптография. Кроме того, он более устойчив в некоторых средах, но обычно не совместим со смартфонами и не соответствует NFC.