
Sådan kopierer du RFID nøglebrikker og adgangskort
Indholdsfortegnelse
Sådan kopierer du RFID nøglebrikker og adgangskort: En komplet vejledning
Men hvad nu hvis du mister din RFID nøgleringe eller har du brug for en ekstra kopi til familien eller personalet? Denne vejledning forklarer, hvordan kopiering fungerer, hvilke chips der kan duplikeres, og hvilke juridiske og sikkerhedsmæssige forholdsregler der skal følges.
Hurtig tjekliste: Sådan fungerer kopiering
Før du går i gang, er her en enkel 4-trins oversigt, du kan følge:
Scan → Skriv → Test → Registrer
- Scan din original RFID nøgleringe ved hjælp af en kompatibel USB RFID-kopimaskine.
- Skriv de gemte data til et tomt RFID-mærke eller -kort.
- Test den nye tag på din dør eller læser.
- Registrer det hos din systemadministrator, hvis det er nødvendigt.
⚠️ Bemærk: Kopier kun RFID-nøglebrikker eller adgangskort, som du ejer eller har tilladelse til at kopiere. Uautoriseret kopiering kan være ulovligt og kompromittere systemsikkerheden.
Hvad er en RFID-nøglebrik, og hvordan fungerer den?
An RFID nøglebrik er en lille trådløs enhed, der bruger radiofrekvensidentifikation (RFID) til at kommunikere med en læser. Når den holdes hen til en læser, sender den et unikt ID-nummer, som adgangssystemet genkender og giver adgang.
Vigtigste funktioner
- Bekvemmelighed: Tap-and-go-adgang uden nøgler.
- Holdbarhed: Tåler daglig brug.
- Tilpasselig adgang: Programmeret til bestemte brugere eller områder.
Disse nøgleringe og RFID kort bruges i lejligheder, kontorer, parkeringssystemer og skoler.
Hvorfor kopiere RFID-nøglebrikker eller adgangskort?
- Bekvemmelighed: Giv familiemedlemmer eller personale deres egne nøglebrikker.
- Sikkerhedskopi: Undgå at blive låst ude, hvis originalen går tabt.
- Delt adgang: Forenkle adgangen for rengøringspersonale, gæster eller korttidslejemål.
At have et ekstra RFID-kort sikrer kontinuerlig adgang uden at skulle vente på erstatningskort.
Forståelse af chiptyper og kopieringsvanskeligheder
Ikke alle RFID-nøglebrikker kan klones. Kopiering afhænger af frekvensen og chiptypen inde i kortet eller brikken.
1. 125 kHz lavfrekvens (LF) – EM4100 / HID Prox
- Almindelig anvendelse: ældre bygningssystemer.
- Kopiering: relativt nemt med en almindelig USB RFID-kopimaskine og tomme 125 kHz-tags.
- Behandle: scanning → skrivning → test → registrering.
2. 13,56 MHz højfrekvens (HF) – MIFARE Classic
- Almindelig anvendelse: kontorer, skoler, transportkort.
- Kopiering: kun muligt, hvis krypteringen er svag eller mangler.
- Værktøjer: en avanceret kopimaskine, der understøtter MIFARE Classic.
3. DESFire / HID iCLASS / SEOS (krypterede smartkort)
- Almindelig anvendelse: virksomheds- eller offentlige systemer.
- Kopiering: typisk ikke muligt uden administratorrettigheder.
- Bedste praksis: Anmod om en officiel kopi fra din ejendomsadministrator.
Tip: Kontroller frekvensmærkaten på dit RFID-kort, eller scan det med en RFID-læser for at identificere chiptypen, inden du forsøger at kopiere det.

Værktøj, du får brug for
For at kopiere en RFID-nøglebrik eller et RFID-kort korrekt skal du forberede følgende:
- RFID-kopimaskine eller -duplikator – til at læse og skrive data.
- Tomme RFID-tags eller -kort – til at oprette nye kopier.
- Original RFID-nøglebrik – kildelegitimationen.
- (Valgfrit) NFC-smartphoneapp – begrænset brug for nogle 13,56 MHz-tags.
Du kan gennemse Blank 125 kHz RFID-tags og RFID-kort til adgangskontrol fra pålidelige leverandører.
Kan jeg kopiere en RFID-nøglebrik med min telefon?
Nogle NFC-kompatible smartphones kan læse og emulere 13,56 MHz RFID-kort, men de kan ikke klone krypterede nøglebrikker.
- Fungerer med: Ubeskyttede MIFARE Classic- eller NTAG-chips.
- Fungerer ikke med: HID iCLASS, SEOS eller DESFire.
- Ekstra hardware: kan være påkrævet for at skrive til fysiske kort.
Sikkerhedsrisici og hvordan man holder sig sikker
Kopiering af RFID-nøglebrikker uden tilsyn kan skabe sikkerhedsproblemer:
- Uautoriseret adgang: duplikater kan misbruges.
- Ukrypterede data: Ældre nøglebrikker er nemmere at klone.
- Datatyveri: usikre læsere kan lække oplysninger.
Bedste praksis: - Brug krypterede eller sikre RFID-kort.
- Skift adgangskoder regelmæssigt.
- Overvåg indtastningslogfiler for usædvanlige mønstre.
Forbedring af sikkerheden ved adgangskontrol
For at styrke dit system:
- Opgrader til krypterede nøglebrikker (MIFARE DESFire eller HID iCLASS).
- Aktivér tofaktorgodkendelse: kombinere RFID med PIN-kode eller biometri.
- Spor brugeraktivitet: bruge softwarelogfiler til at opdage uregelmæssigheder.
“En korrekt krypteret RFID-nøglebrik reducerer risikoen for kloning og beskytter hele din facilitet.”
RFID vs. NFC: Hurtig sammenligning
| Feature | RFID | NFC |
|---|---|---|
| Rækkevidde | Op til flere meter | Et par centimeter |
| Typisk anvendelse | Adgangskontrol, logistik | Mobilbetalinger, smartcards |
| Duplikationsvanskeligheder | Moderat til høj | Meget høj (på grund af kryptering) |
Begge bruger radiofrekvens, men NFC er mere sikker og bruges typisk til smartphones og betalingssystemer, mens RFID-nøglebrikker er optimeret til døråbning og identifikation.
Kryptering i moderne RFID-kort
Kryptering beskytter kommunikationen mellem RFID-kortet og læseren, hvilket gør uautoriseret kopiering næsten umulig.
Fordele:
- Forhindrer duplikering af data.
- Bevarer dataintegriteten.
- Gør dit system fremtidssikret mod angreb.
Overgang til krypterede RFID-kort er en af de nemmeste måder at forhindre uautoriserede kopier på.
Ofte stillede spørgsmål om RFID nøglebrikker og adgangskort
Hvordan kan jeg se, om min nøglebrik er krypteret?
Krypterede nøglebrikker kræver normalt proprietær software eller specielle læsere. Hvis en almindelig kopimaskine ikke kan læse den, er den sandsynligvis krypteret.
Kan jeg kopiere en RFID nøglebrik derhjemme?
Ja, det kan du med en kompatibel RFID-kopimaskine og tomme tags, men kun hvis du har tilladelse til at kopiere dem.
Hvad er forskellen mellem RFID og NFC?
RFID har en længere rækkevidde og flere frekvensbånd; NFC har kort rækkevidde og bruges hovedsageligt i smartphones.
Er det lovligt at kopiere et RFID-adgangskort?
Uautoriseret kopiering kan være i strid med reglerne om privatlivets fred eller ejendomsret. Indhent altid tilladelse fra systemets ejer.
Hvad er de almindelige frekvenser?
125 kHz (LF) og 13,56 MHz (HF) er mest almindelige for nøglebrikker og adgangskort.
Konklusion
RFID-nøglebrikker og adgangskort er effektive værktøjer til sikkerhed og bekvemmelighed — men for at kopiere dem kræves der kendskab til chiptyper, værktøjer og lovmæssige begrænsninger.
Hvis du er i tvivl, skal du søge hjælp hos en certificeret RFID-tekniker eller anmode om en officiel udskiftning fra din bygningsadministration.
Har du brug for pålidelige RFID-nøglebrikker, adgangskort eller kopimaskiner til dit projekt?
Tal med vores RFID-eksperter for prøver, priser eller teknisk rådgivning.
📩 Send os en e-mail på [email protected]

Ray Zhou
Denne artikel er skrevet af Ray Zhou, en ekspert i RFID-teknologi med mere end 10 års brancheerfaring.
Kommentarer
Hotte produkter
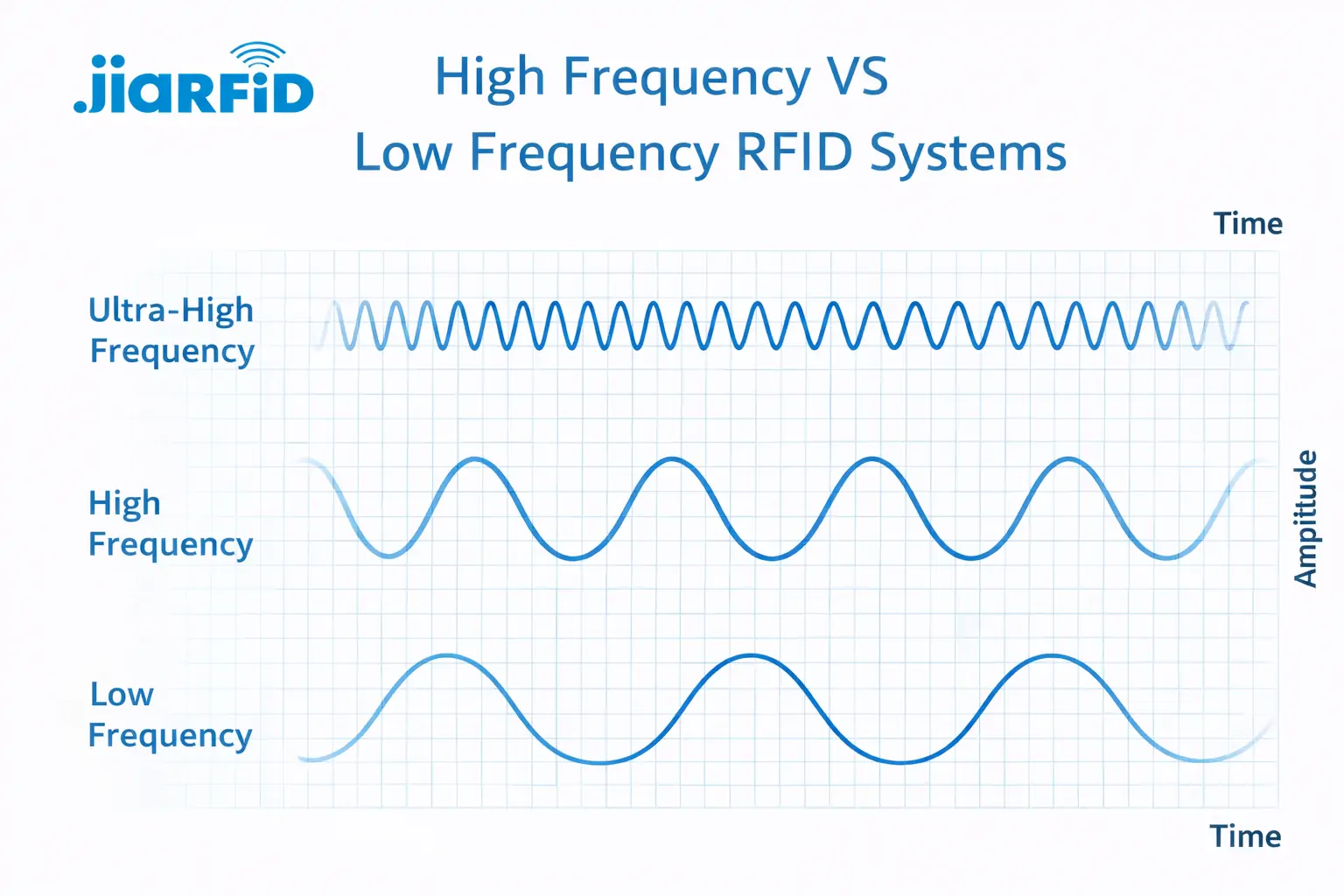
Lavfrekvent RFID vs. højfrekvent RFID: De vigtigste 14 forskelle
Lavfrekvens-RFID og højfrekvens-RFID er begge induktive RFID-teknologier, der er afhængige af magnetfeltkobling mellem
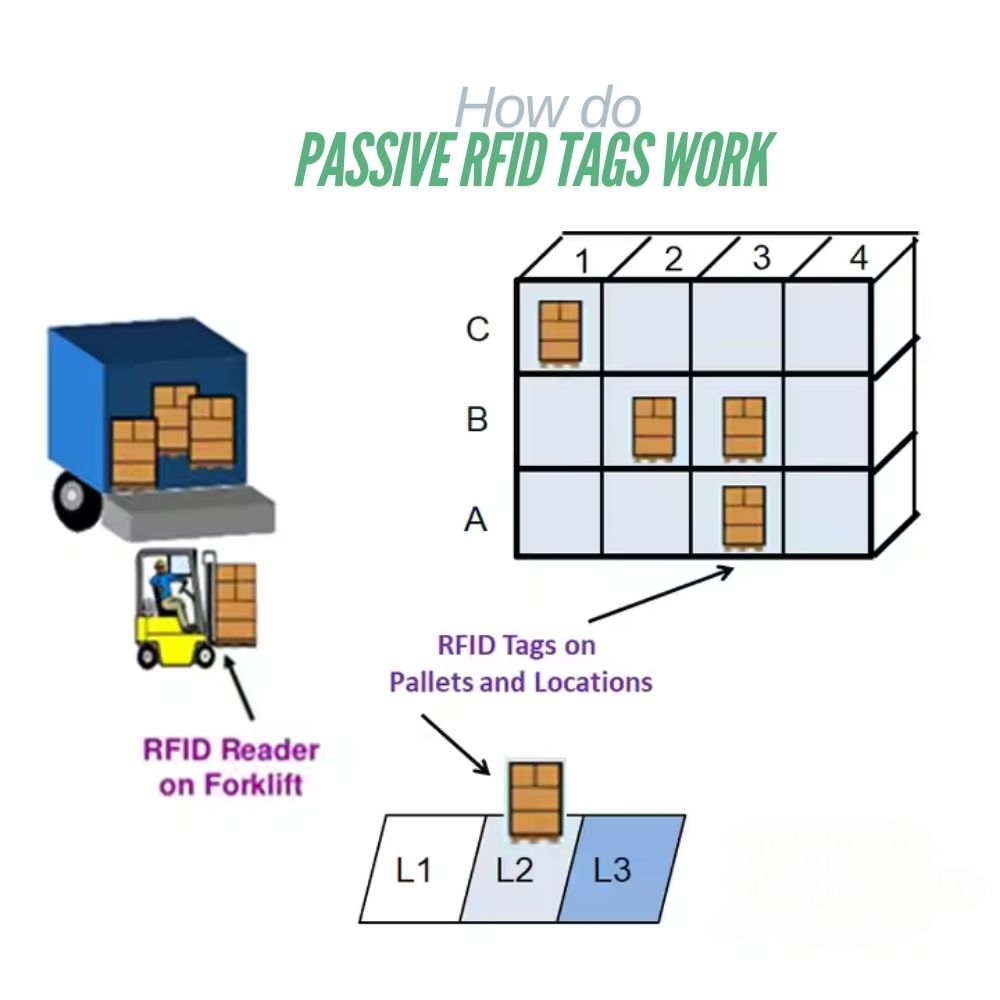
Hvad er passive RFID-tags, og hvordan fungerer de?
Et passivt RFID-tag er et RFID-tag, der ikke har nogen intern strømkilde. Det kan ikke køre eller sende ved hjælp af

13,56 MHz RFID-kort og -tags forklaret: Alt hvad du bør vide
RFID-teknologien spiller en vigtig rolle i moderne identifikations- og dataudvekslingssystemer. Blandt de forskellige RFID-frekvenser er 13,56 MHz
RFID i logistik: Sådan undgår du fejl i RFID-ruteplanlægning og fejl i RFID-mærker
RFID i logistikken er mere end blot et værktøj til at fremskynde processer. Det er blevet en central del af, hvordan moderne forsyningskæder fungerer.
Hvad er RFID-affaldshåndtering?
Forestil dig en by, hvor alle skraldespande taler – ikke bogstaveligt talt – men via en lille chip, der fortæller systemet, når de er fulde, når de er tømt, og hvor de er blevet kørt hen. Det er netop det, RFID-affaldshåndtering gør i dag.

Hvad er boltetætninger og deres anvendelser? | Komplet guide
Inden for global handel og logistik spiller boltforseglinger en afgørende rolle for fragtsikkerhed og compliance. Disse små, men kraftfulde enheder er designet til at låse skibscontainere, trailere og fragtdøre med en mekanisme, der sikrer mod manipulation.
Tags
RELATEREDE BLOGS
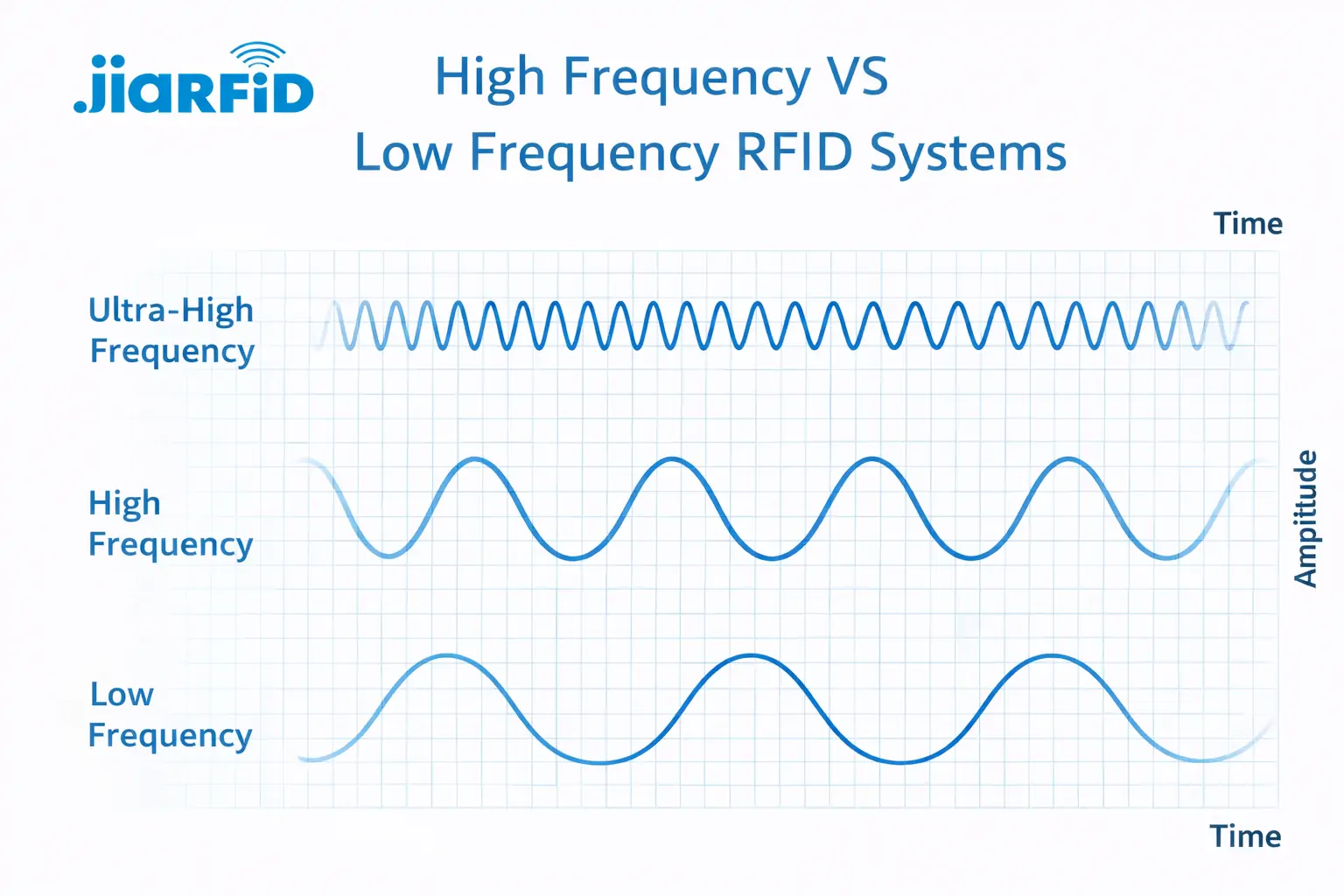
Lavfrekvent RFID vs. højfrekvent RFID: De vigtigste 14 forskelle
Lavfrekvens-RFID og højfrekvens-RFID er begge induktive RFID-teknologier, der er afhængige af magnetfeltkobling mellem
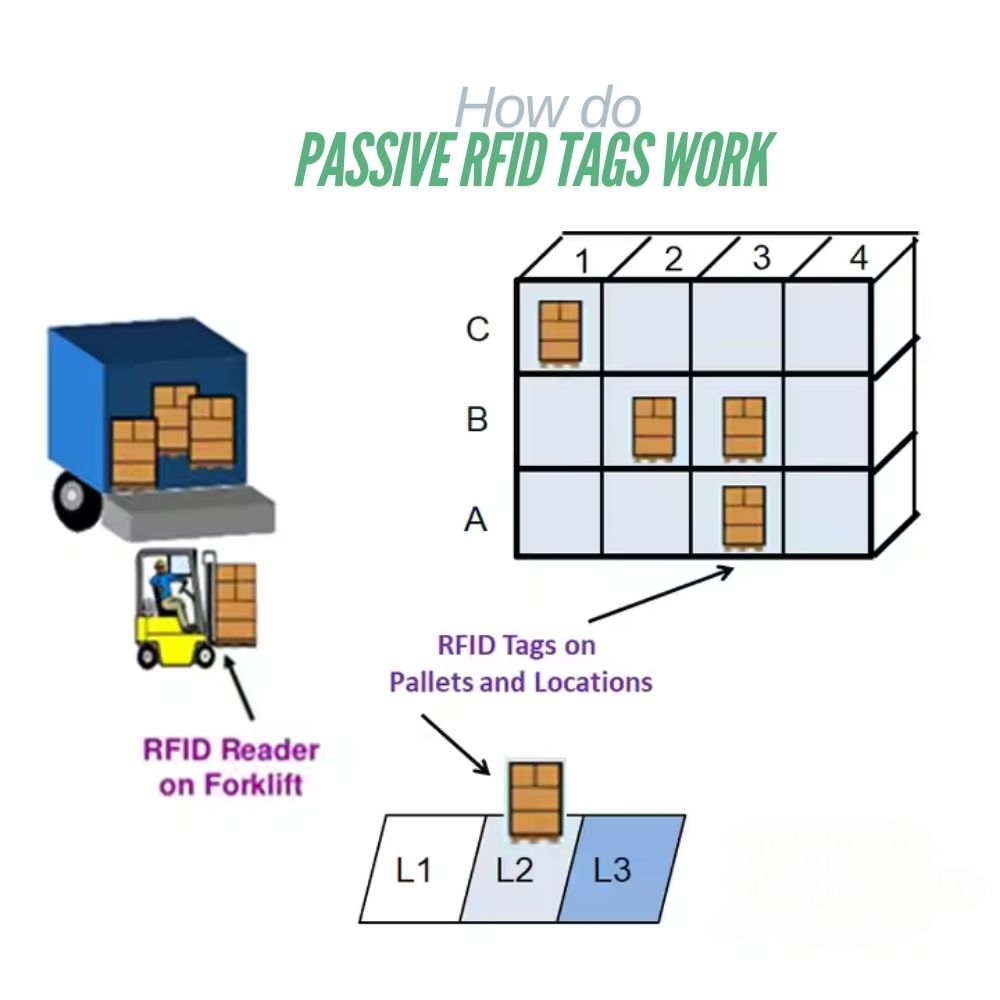
Hvad er passive RFID-tags, og hvordan fungerer de?
Et passivt RFID-tag er et RFID-tag, der ikke har nogen intern strømkilde. Det kan ikke køre eller sende ved hjælp af

13,56 MHz RFID-kort og -tags forklaret: Alt hvad du bør vide
RFID-teknologien spiller en vigtig rolle i moderne identifikations- og dataudvekslingssystemer. Blandt de forskellige RFID-frekvenser er 13,56 MHz




